Recent research by Citizen Lab uncovers two sophisticated telecom surveillance campaigns, linking real-world attack traffic to the signaling infrastructure of mobile operators for the first time.
The findings of these researchers demonstrate how companies suspected to be commercial surveillance vendors (CSVs) exploit the global telecommunications interconnect ecosystem, abuse operators’ private networks, and conduct covert location tracking operations in a manner that can remain undetected for years.
Key Research Findings
-
- Multi-Vector Surveillance: Citizen Lab researchers have identified actors utilizing multiple techniques to track their targets by combining 3G and 4G signaling network protocols with direct device exploitation via SMS.
- SIM Card Abuse: In one of the campaigns, a malicious SMS containing hidden SIM card commands was sent to extract location information; an attempt to turn the victim’s device into a covert tracking beacon.
- Sophisticated and Customized Tools: Both threat actors employed proprietary surveillance tools to spoof operators, manipulate signaling protocols, and steer traffic through specific paths in the interconnect network to bypass defenses and obscure attribution.
- Global-Scale Network Infrastructure: These attacks leveraged identifiers and infrastructure associated with operators worldwide, including networks based in the UK, Israel, China, Thailand, Sweden, Italy, Liechtenstein, Cambodia, Mozambique, Uganda, Rwanda, Poland, Switzerland, Morocco, Namibia, Lesotho, and the self-governing island of Jersey, highlighting the vast scope and global reach of these operations.
- Persistent and Long-term Activities: Telemetry shared by mobile signaling security provider (Cellusys) indicates that operator identifiers have been repeatedly used over several years, forming persistent clusters that have enabled the execution of long-term surveillance operations.
- Weak OPSEC in Intercarrier Providers: Poor filtering and monitoring of interconnect traffic have allowed attackers to route their surveillance messages through trusted operator pathways and gain access to target networks.
Introduction
In recent years, numerous investigations have exposed the vulnerabilities present in the mobile communications ecosystem and how state security agencies abuse them to track targets abroad (while roaming). These studies include several previous reports by Citizen Lab and the contributions of other researchers. This new research builds upon those findings, delving deeper into the structural weaknesses that continue to provide a breeding ground for the development and evolution of targeted surveillance.
In late 2024, following the identification of a series of anomalous events in signaling firewall logs and receiving supplementary information from the security firm Cellusys, Citizen Lab researchers initiated an investigation into coordinated location tracking activities. What initially appeared to be a limited incident against a single mobile subscriber evolved into a broader investigation that uncovered the campaigns of two distinct commercial surveillance vendors (CSVs); campaigns conducting long-term espionage operations by exploiting the global telecommunications ecosystem.
The first campaign, observed in November 2024, involved a multi-stage effort to track a high-profile subscriber using several 3G and 4G networks. Information provided by the target user’s network operator indicated that the mobile number belonged to a well-known executive, referred to as a “VVIP” (Very Very Important Person). This context demonstrated that the user was a high-value surveillance target.
In early 2025, the research team identified another coordinated tracking event conducted using a specially formatted SMS. Although these two campaigns were technically distinct, both exhibited sophisticated, structured, and repeatable methods that perfectly align with purpose-built surveillance platforms.
Citizen Lab’s collaboration with mobile industry partners enabled a comprehensive review using signaling log metadata, packet captures, routing data, and other telecommunication sources to trace the methods and origins of these advanced surveillance activities. This analysis identified 4G infrastructure associated with operator networks in Israel, the UK, and the Channel Islands. Interestingly, previous public reports have also identified these exact countries as the origins of commercial surveillance vendors (CSVs) targeting mobile users.
The findings of this report highlight a systemic problem at the core of global telecommunications: operator infrastructures designed to create seamless international connectivity are now being abused to support covert surveillance operations; operations whose monitoring, attribution, and regulation are exceedingly difficult. Despite repeated public reports, these activities continue relentlessly and without consequence. The continued use of mobile networks, which rely on the “inter-operator trust model” and upon which users worldwide depend, raises broader questions for national regulators, policymakers, and the telecommunications industry regarding accountability, oversight, and global security.
Methodology
This report is based on collaborative analysis with several companies active in the telecommunications industry, including signaling firewall provider (Cellusys), international signaling network provider (Telenor Linx), telecom data intelligence provider (Roaming Audit), and telecom network security company (P1 Security).
Citizen Lab researchers validated their investigation by cross-referencing signaling data with independent and complementary data sources; an approach that enabled precise analysis of how messages were sent, routed, and delivered across the global interconnect ecosystem. These sources included the following:
- Mobile network configurations extracted from GSMA industry files
- Telecommunications Domain Name System (DNS) records
- Border Gateway Protocol (BGP) routing data and Autonomous System Number (ASN) registries
- Publicly available records and logs from national telecom regulatory bodies
The research team applied a multi-stage analytical process for the attribution of the observed surveillance activities to distinct threat actors, which involved identifying, clustering, and matching suspicious indicators across the campaigns.
Analytical Approach
1. Detecting Suspicious Signaling Activities
The research team identified commands within international signaling traffic that corresponded to known surveillance techniques in 3G SS7 and 4G Diameter signaling protocols. Although some of these commands also have legitimate and lawful applications, their repeated and patterned use is typically associated with espionage and surveillance activities.
2. Identifying Surveillance Campaign Patterns
Network traffic was analyzed to detect repeated commands over short time intervals from individual operator signaling addresses. Subsequently, coordinated activities across multiple operators that matched this behavior within the same timeframe were identified. These temporal and behavioral patterns were utilized to isolate distinct surveillance campaigns.
3. Target Validation
Cellusys confirmed that each campaign targeted specific subscriber identities (IMSIs). By correlating the timing and sequence of the location tracking attempts, they verified consistent targeting patterns across multiple operator identifiers.
4. Actor Fingerprinting
Researchers identified distinct surveillance actors by technically fingerprinting their signaling characteristics. They looked for indicators such as sequential or patterned Transaction Identifiers, non-standard message formats, parameter configurations, reuse of operator identifiers, and consistent routing behaviors.
5. Infrastructure Mapping and Routing Analysis
The Citizen Lab team cross-referenced operator identifiers with external data sources, including operators’ IR.21 roaming files, ASN and IP address allocations, BGP routing data, and DNS records. This allowed them to accurately map how attack traffic entered and traversed the signaling interconnect ecosystem.
6. Historical Correlation
The researchers’ final step was to correlate the observed attack indicators with historical telemetry to gauge the duration of the campaign and the extent to which a specific operator’s infrastructure was repeatedly used over several years.
Limitations and Attribution of Attacks
It is crucial to note that the operator signaling addresses observed in these attacks do not necessarily imply the direct and intentional involvement of that operator. In many cases, access to the signaling ecosystem can be obtained through third-party providers, commercial leasing agreements, or other intermediary services that allow threat actors to send their messages using the operator identifiers of legitimate and valid networks.
This analysis merely examines how signaling infrastructure was abused in the attack campaigns, not the intent of the operators or network providers. Although Citizen Lab researchers do not directly attribute the attacks discussed in this report to a specific government or organization, numerous indicators point to the likely involvement of a commercial surveillance platform supporting state-sponsored intelligence activities.
The Persistence of Lost Trust in Mobile Communications
To understand how the attacks described in this report occurred, it is necessary to examine how mobile networks communicate with each other and the operational landscape that facilitates these communications. The system that connects mobile operators worldwide for international travel and mobile services uses a combination of protocols, including SS7 (known for older 3G networks) and Diameter (for 4G and most 5G networks). Although SS7 has long been considered a legacy protocol, it still plays a vital role in international roaming, SMS, and emergency services. This hybrid ecosystem of vulnerable protocols creates amplified opportunities for surveillance actors.
These vulnerabilities do not stem from software bugs or network misconfigurations; rather, they are rooted in the fundamental design and commercial practices of global telecommunications. The mobile ecosystem comprises over a thousand operators interconnected through roaming agreements and signaling protocols; protocols that prioritize efficiency, service availability, and revenue-generation opportunities over security. As a result of this approach, a shadowy marketplace of commercial and state-sponsored espionage actors has emerged, developing and deploying specialized software platforms to weaponize telecommunications networks for global surveillance.
Insecure by Design
The root of this security problem lies within the foundational signaling protocols themselves. SS7 protocols, originally designed for a closed, trusted community of mobile operators and vetted third-party service providers, lack the basic security mechanisms of IP networks; mechanisms such as authentication and validation to verify the origin of signaling messages, integrity checks to ensure data has not been altered, and encryption to protect message content.
The Diameter protocol, currently used in international 4G roaming deployments and most 5G networks, was designed with stronger security controls than SS7 and introduced new security components to address the inherent vulnerabilities of signaling. These include support for TLS (Transport Layer Security) and IPsec encryption to protect signaling traffic, as well as authentication between operator networks.
However, in practice, operators have largely fallen short in implementing these protective layers, relying instead on the same “Peer-to-Peer Trust Model” that plagues SS7. Furthermore, key operational security measures—such as verifying that the network’s security configurations align with the published information from the roaming partner network in GSMA IR.21 documents—are rarely enforced. As a result of these oversights, security research has shown that 4G networks remain vulnerable to many of the same user-centric surveillance techniques associated with 3G.
What is an IR.21 file?
An IR.21 document is a documented specification shared among mobile operators via the GSMA. This file contains technical and operational details about an operator’s network, such as network codes, signaling address ranges and network allocations, interconnect details, and other information necessary for managing international roaming services.
Attackers with access to IR.21 data can exploit it to identify network elements or craft signaling messages that appear completely legitimate and valid within the global telecommunications ecosystem.
Actors who gain access to the global signaling ecosystem (through commercial agreements with mobile operators, breaching telecommunication nodes, and seizing control of telecom networks) can send signaling commands to networks worldwide. Since these protocols do not authenticate the true source of the commands, malicious signaling traffic can be spoofed to appear as though it originated from legitimate nodes within an operator’s network. This security loophole enables location tracking, Denial of Service (DoS) attacks, or traffic redirection toward attacker-controlled infrastructure.
In practice, access to the signaling backbone is not restricted solely to Mobile Network Operators (MNOs). A wide range of service providers maintain their connections to intercarrier networks to offer services such as HLR Lookup, domestic and international messaging, roaming hubs, and Mobile Virtual Network Enabler (MVNE) services. These third-party platforms, which connect directly to intercarrier providers, typically generate and send SS7 and Diameter signaling queries on behalf of their commercial clients. Attackers who purchase the services of these third-party providers and connect to their platforms can acquire an indirect channel to enter the private signaling ecosystem.
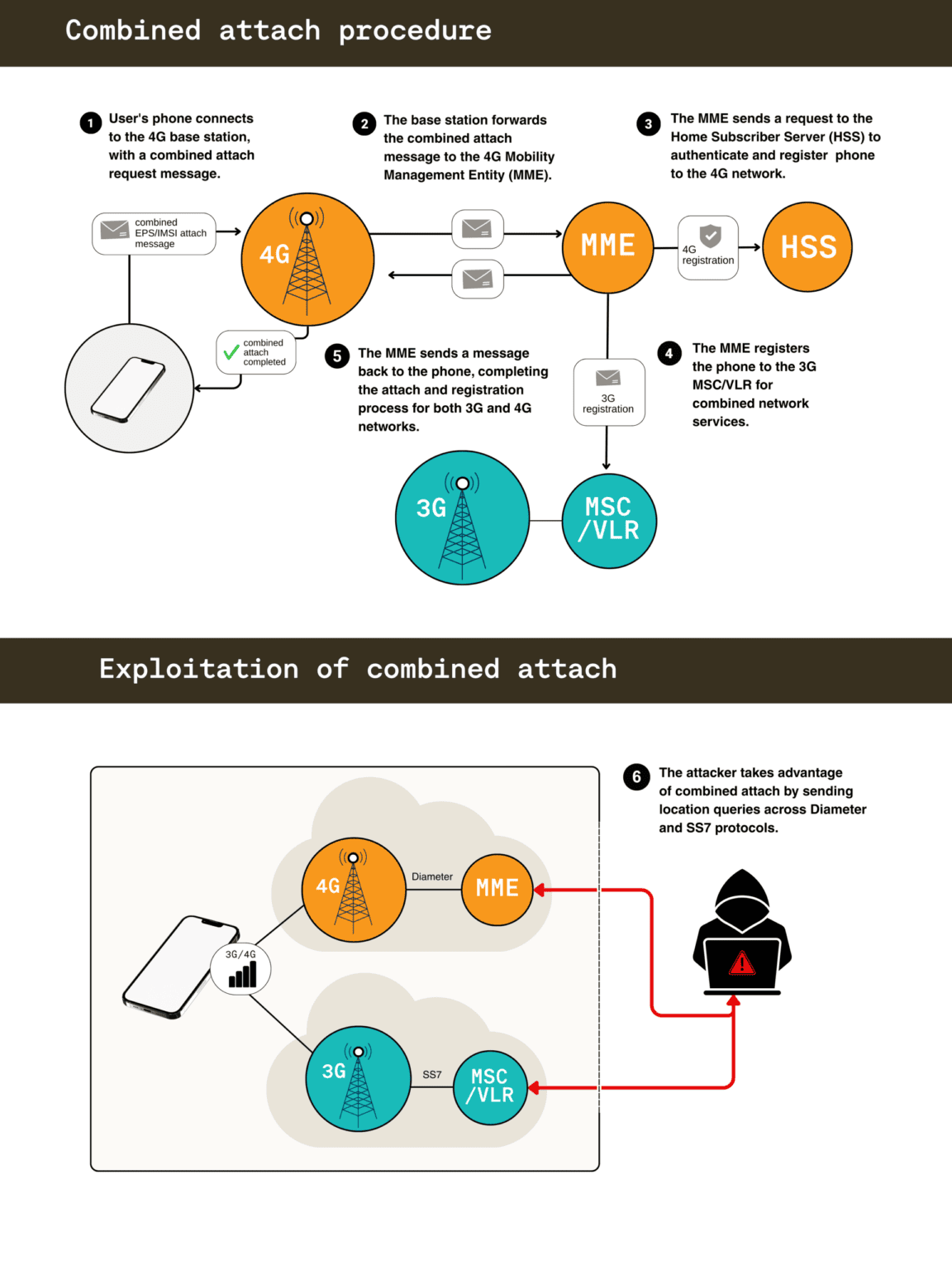
Additional security risks also stem from the interoperability between modern 4G/5G networks and legacy 3G systems. Operators that have deployed both networks support a procedure known as Combined Attach, which allows a roaming device to simultaneously register on both 3G and 4G networks to maintain service continuity and fallback connectivity.
Attackers with access to both 3G and 4G signaling environments can exploit this dual registration feature and pivot their attacks seamlessly between Diameter and SS7 protocols. By switching between these two signaling systems, attackers gain the upper hand when operators lack firewall protections against these advanced, cross-protocol attacks. Consequently, the insecurity of legacy SS7 protocols becomes a significantly more dire situation for sophisticated actors capable of utilizing both attack vectors.
Telecom Surveillance Actors: A Crowded and Shadowy Market
For over a decade, researchers have documented how threat actors exploit network vulnerabilities in SS7 and Diameter signaling. However, executing attacks on a massive scale requires the complex integration of multiple signaling protocols into a Command-and-Control (C2) system capable of operating across global telecommunications networks. This technical and operational complexity demands deep engineering expertise, specialized tools, and privileged access to private mobile network infrastructure.
These requirements are only within the reach of a relatively small number of well-resourced actors. The telecom surveillance ecosystem consists of two overlapping groups: state-linked espionage services that conduct Signals Intelligence operations through telecommunications networks, and commercial surveillance vendors (CSVs) that develop and sell interception and tracking services to government clients (as shown in Table 1). The diversity and persistence of the observed telecom attacks indicate that both groups play an active role in exploiting these vulnerabilities.
| Group / Company Name | Affiliation | Reported Telecom Surveillance Activities |
|---|---|---|
| State-Sponsored Espionage Actors | ||
| Salt Typhoon | China’s Ministry of State Security (MSS) | Associated with cyber espionage campaigns targeting telecommunications infrastructure and government officials in multiple countries. |
| Liminal Panda (LightBasin) | China-linked espionage actor | Known for infiltrating telecom operator networks to collect subscriber information, call metadata, and SMS messages using custom signaling tools. |
| MuddyWater | Iran’s Ministry of Intelligence (MOIS) | Executing cyber operations targeting telecommunications service providers in Africa and the Middle East. |
| Commercial Surveillance Vendors (CSVs) | ||
| Circles, Cognyte, Rayzone, Defentek | Various | Detailed in a February 2024 letter from U.S. Senator Ron Wyden to the U.S. President requesting sanctions against several telecom surveillance companies. |
| RCS Lab / Tykelab (Cy4gate) | Italy | Providers of hybrid surveillance platforms that combine device spyware with telecom signaling monitoring capabilities. |
| Fink Telecom Services (FTS) | Switzerland | A telecom company reported to have leased SS7 Global Titles and provided location tracking and interception capabilities. |
| Rayzone Group | Israel | Investigative reports have linked this company to leasing telecom signaling access from operators in Jersey, Guernsey, and other networks. |
Examples of State-Sponsored and Commercial Espionage Actors in the Telecom Sector.
While most commercial threat groups focus on device implants (spyware installed on phones), there is strong demand from government agencies for “off-the-shelf” telecom surveillance services; services that use mobile networks to locate, track users, and intercept communications without the need to hack the target’s phone. These services are often provided through intermediaries who have direct or indirect access to operator networks or service providers, allowing surveillance traffic to blend in with legitimate roaming traffic.
The Hidden Layer of Global Surveillance
Unlike typical cyber campaigns, telecom-level surveillance is almost invisible to the broader security community. Attacks occur within a closed ecosystem of mobile operators, telecom equipment vendors, and mobile interconnect providers, which are largely inaccessible to the cybersecurity research community. This lack of transparency means that attacks are rarely exposed publicly, and the techniques and infrastructure used for real-world telecom espionage often remain hidden.
This situation makes the restricted telecom ecosystem an ideal environment for espionage operations. Signaling messages traverse private international roaming networks, and even when firewalls are deployed, enforcement is often inadequate, creating a blind spot that surveillance actors have used to continue their activities undetected for years.
This hidden signaling layer also allows attackers to masquerade as trusted operators by using legitimate signaling identifiers and interconnect providers. When operators provide third-party access to their infrastructure through commercial leasing agreements, surveillance operations assume the identity of that operator, obscuring the attribution of the attack to the primary actor.
These practices, which provide third-party access to operator infrastructure without oversight or security safeguards, empower surveillance actors and cause real harm to civil society. Previous Citizen Lab investigations have documented how the telecommunications ecosystem facilitates the incentives and drivers for location-tracking-based surveillance. This now mature and unregulated marketplace has become a primary enabler for espionage, where direct attribution of attacks to state or non-state actors is exceedingly difficult.
Network Ghosts: Tracking the Origin of Attacks in Mobile Networks
Historically, operators initially deployed SS7 firewalls, designed to block unauthorized signaling messages from external networks, in response to public reports about SS7 location tracking attacks and security guidelines issued by the GSMA. Over time, operators also deployed Diameter firewalls to counter threats in 4G networks. However, industry reviews show that the operator firewall deployment process has been slow, and there are limited protections against more advanced attacks that employ a combination of 3G and 4G network techniques simultaneously.
The campaigns analyzed by Citizen Lab researchers in this report demonstrate how espionage actors exploit these security gaps by using legitimate operator signaling identifiers to send location queries through the global interconnection system. In some cases, these identifiers appear to have been acquired through commercial agreements or intermediary service providers; in other cases, they appear to have been spoofed to masquerade as legitimate operator infrastructure. Because the mobile roaming ecosystem relies on trusted communication between operators, these attacks are designed to appear as though they originated from legitimate networks.
These techniques allow surveillance actors to operate as what researchers term “Ghost Operators”. They appear as completely legitimate and valid originating operators while remaining invisible by hiding behind operator identities and entering the private signaling backbone.
As detailed in subsequent sections of the report, these actors have employed several techniques to maintain access and evade detection. These techniques included shifting between SS7 and Diameter protocols, rotating signaling identifiers associated with various operator networks, and manipulating routing paths to steer messages through specific intercarrier providers. By doing so, they can maintain the persistence of their access by blending attack traffic with background roaming traffic.
Operationalizing these techniques requires access to routable signaling identifiers; identifiers assigned to operators by national telecom regulatory bodies and published in IR.21 documents to support global roaming. In practice, as has been revealed, this access can be obtained through commercial agreements and intermediary service providers.
Because these attacks rely on legitimate operator identities, tracing their origin requires sufficient visibility into how signaling identifiers are used and how messages traverse the ecosystem. By analyzing firewall telemetry, routing traces, and interconnection metadata, the Citizen Lab research team mapped how attack messages entered the signaling backbone and reached target networks. This analysis reveals how surveillance actors operationalize and execute access to mobile network infrastructure while concealing their point of origin.
Signaling and Routing Indicators: Why the Path Matters
Understanding how attackers exploit the mobile signaling ecosystem requires looking at how signaling traffic moves between operators. Normally, operators send signaling traffic through a global network of service providers; a network that exchanges messages between operator networks supporting roaming services.
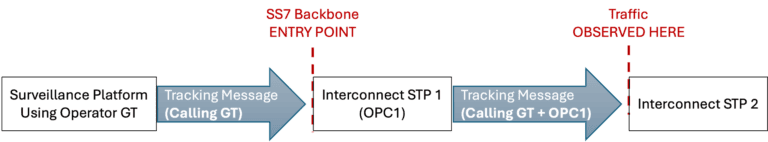
In SS7 networks, signaling messages are routed using Global Title (GT) addresses, which are assigned to operators by national telecom regulators. When a message is sent, it contains the Calling Party GT. That message is forwarded through intermediary routing nodes called Signalling Transfer Points (STPs), which are operated by interconnect providers. Each STP is identified by a unique node identifier called a Point Code (PC).
As messages are sent across the signaling backbone, the STP that forwards the message to the next hop is identified by the Originating Point Code (OPC) field. By observing the message OPCs at the first transit point entering the SS7 backbone, researchers can determine whether the network provider sending surveillance messages differs from what the operator reported in its IR.21 roaming document (this concept is illustrated in Figure 2 of the report).
In contrast, 4G networks deliver Diameter signaling via IP Exchange (IPX) providers using hop-by-hop IP-based routing; in this method, addresses formatted as Hostname + Domain are used to identify mobile operators.
The Origin-Host attribute in the Diameter protocol identifies the sending node, and the target operator’s network is identified by the Destination-Realm attribute.
While the OPC identifies transit points in the SS7 network, the Route-Record attribute in Diameter identifies each relay point along the Diameter path to ensure that the Submit and Response paths remain consistent and aligned. An overview of network identifier formats is provided in Table 2 below.
| Network Identifier | Format | Use in International Mobile Networks |
|---|---|---|
| SS7 Global Title (GT) Address | Country Code (CC) + National Destination Code (NDC) + Subscriber Number (SN) |
Routing SS7 signaling messages between operators using the SCCP protocol. Note: The “Subscriber Number” (SN) portion here identifies a network node, not the user’s phone number. |
| Origin-Host | hostname.epc.mnc<MNC>.mcc<MCC>.3gppnetwork.org |
Identifies the endpoint that sent the Diameter message. |
| Origin-Realm | epc.mnc<MNC>.mcc<MCC>.3gppnetwork.org |
Identifies the network sending the Diameter message so the response returns along the same path. |
| Route-Record | hostname.epc.mnc<MNC>.mcc<MCC>.3gppnetwork.org |
Contains the Hostname of the node relaying the message along the path. |
| Destination-Realm | epc.mnc<MNC>.mcc<MCC>.3gppnetwork.org |
Identifies the target operator’s network for the sent message. |
Description of Key Signaling Network Identifiers.
To understand how SS7 attack traffic entered the signaling backbone, Citizen Lab researchers compared the expected routing paths (based on operators’ IR.21 files) with the observed paths via GTs in real signaling traffic. Under normal circumstances, an operator’s traffic should route through the interconnect providers listed in that same operator’s IR.21 file.
A key finding in the organization’s analysis was the discovery of frequent mismatches between the expected providers and the providers actually observed sending attack traffic; this indicates that surveillance messages entered the signaling backbone through alternative providers.
By correlating the OPC values in the traffic with the International Telecommunication Union’s (ITU) ISPC allocations, researchers found that the attack traffic consistently passed through interconnect providers with no affiliation to the originating operator. This finding clearly demonstrates the threat actors’ use of a “third party” to send surveillance queries into the signaling network. Table 3 compares the expected interconnect providers (published in IR.21 files) with the OPC of the providers seen in the attack traffic. These routing mismatches reveal the likely use of a third-party entry point into the SS7 backbone.
| Attacking GT | Mobile Operator | Expected Provider (IR.21) | Expected OPC | Provider Observed in Attack Traffic | Observed OPC | Routing Status |
|---|---|---|---|---|---|---|
| 855183901014 | SEATEL (Cambodia) | Comfone AG | 4590/4591 | BICS | 4201/4215 | ❌ Mismatch |
| 855180015170 | SEATEL (Cambodia) | Comfone AG | 4590/4591 | Comfone AG | 4590/4591 | ✅ Match |
| 25882200300 | Tmcel (Mozambique) | Deutsche Telekom | 5091/5092 | BICS | 4201/4215 | ❌ Mismatch |
| 85513000755 | CADCOMMS (Cambodia) | Comfone | 4590/4591 | Tata Communications | 6233 | ❌ Mismatch |
| 46764753182 | Telenabler AB (Sweden) | Comfone | 4590/4591 | Tata Communications | 6184/6233 | ❌ Mismatch |
| 393358840745370 | TIM (Italy) | Telecom Italia Sparkle | 4466 | Telecom Italia Sparkle | 4466 | ✅ Match |
| 25671000036 | Utel (Uganda) | BICS | 4201/4215 | BICS | 4201/4215 | ✅ Match |
| 423790105844 | FL1 (Liechtenstein) | A1 Telekom Austria | 4616 | A1 Telekom Austria | 4616 | ✅ Match |
| 250730091970 | Airtel (Rwanda) | BICS | 4201/4215 | BICS | 4201/4215 | ✅ Match |
| 467647531812 | Telenabler AB (Sweden) | Comfone AG | 4590/4591 | Telia Sweden | 4745 | ❌ Mismatch |
Mismatches of interconnect providers observed in attack traffic.
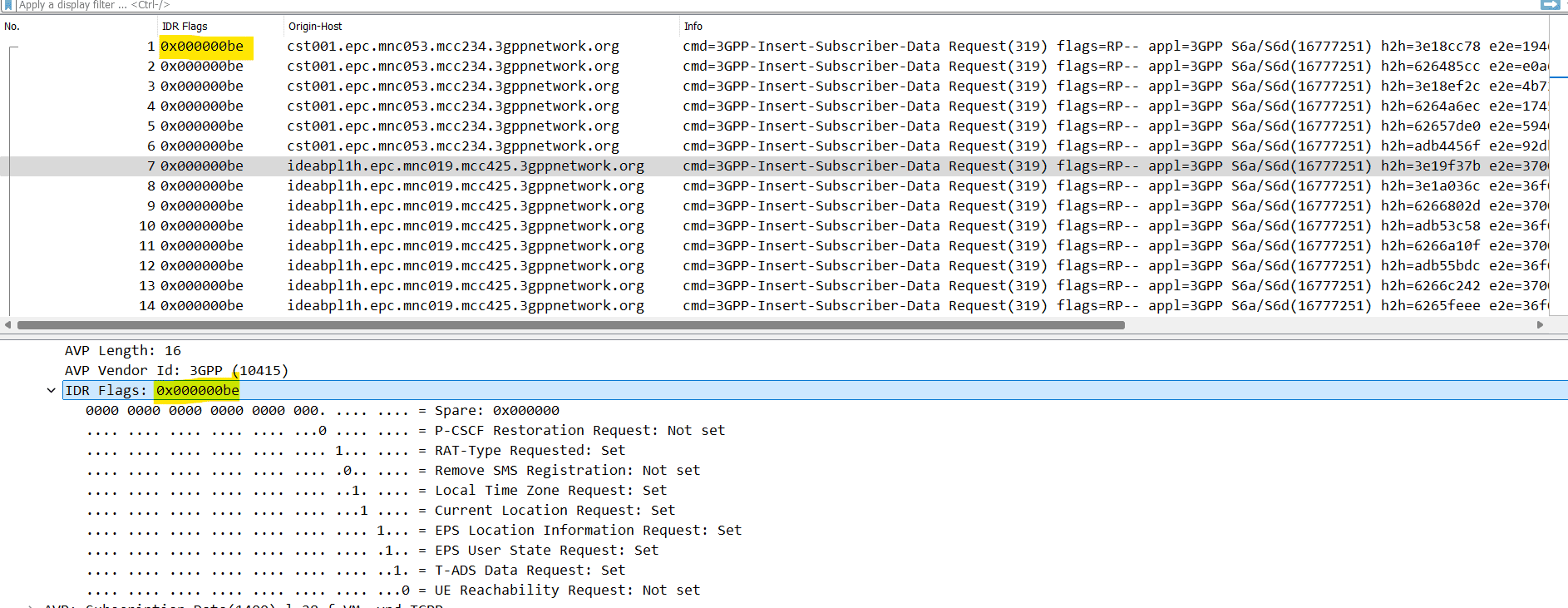
To understand how 4G surveillance messages were routed and delivered to targets, researchers analyzed the Diameter message headers obtained from signaling firewall logs. The headers and routing identifiers present in these logs enabled the research team to trace the message transmission path.
They initially examined the Origin-Host, Origin-Realm, and Route-Record attributes within the surveillance message headers. The identifiers in these fields record the Hostnames and intermediary routing nodes involved in forwarding the messages. Then, using IR.21 documents, BGP routing data, and DNS Zone record sources, they matched and attributed these Hostnames to specific operator networks and IPX providers.
Evidence obtained from the logs showed that both threat actors spoofed operator Hostnames in the Origin-Host field to bypass the target operator’s firewall controls. Furthermore, an operator Hostname was injected into the interconnect routing path, indicated in the Route-Record attribute; an act that exposed the true source of the operator network used in the surveillance campaigns.
Citizen Lab researchers also noticed that one of the actors used a unique Hostname to identify the IPX provider; a provider selected for the transport of a specific attack signaling message. Details regarding the Origin-Hosts and corresponding IPX providers responsible for routing the attack messages are summarized in Table 4.
| Origin-Host Operator | Route-Record 1 | Proxy Operator | Route-Record 2 Hostname | IPX Provider Used |
|---|---|---|---|---|
| Tango Networks UK | cst001.epc.mnc053.mcc234.3gppnetwork.org |
Tango Networks UK | dra01 |
Tango Networks (Hosted by BICS) |
| 019 Mobile Israel | vdrap1.epc.mnc019.mcc425.3gppnetwork.org |
019 Mobile | dranl02 |
Comfone AG |
| AIS Thailand | vmdra01.epc.mnc019.mcc425.3gppnetwork.org |
019 Mobile | ams-01.dra.ipx |
Syniverse Technologies |
| Movitel Mozambique | dra1.je211.epc.mnc003.mcc234.3gppnetwork.org |
Jersey Airtel | dranl01 |
Comfone AG |
| MTS Namibia | dra1.je211.epc.mnc003.mcc234.3gppnetwork.org |
Jersey Airtel | draus01 |
Comfone AG |
| Econet Lesotho | dra1.je211.epc.mnc003.mcc234.3gppnetwork.org |
Jersey Airtel | draus01 |
Comfone AG |
| Inwi Morocco | dra1.je211.epc.mnc003.mcc234.3gppnetwork.org |
Jersey Airtel | draus01 |
Comfone AG |
| Sunrise Switzerland | dra1.je211.epc.mnc003.mcc234.3gppnetwork.org |
Jersey Airtel | draus01 |
Comfone AG |
| Polkomtel Poland | dra1.je211.epc.mnc003.mcc234.3gppnetwork.org |
Jersey Airtel | draus01 |
Comfone AG |
4G/Diameter originating operator hostnames and route records.
Fingerprinting Telecom Surveillance Actors
To distinguish the surveillance campaigns identified in this investigation, researchers analyzed recurring indicators in the signaling traffic and historical attack telemetry. By correlating repeated activities with the headers observed in the attack messages, they were able to identify the technical fingerprints and indicators associated with each actor’s surveillance tools.
In this report, “fingerprinting” refers to the technical details observed across attacks that indicate the use of a common surveillance platform and/or an identical operational methodology. When multiple such details appear across different events, they reveal a consistent pattern, allowing the attacks to be clustered and attributed to a single actor.
1. Manipulation of Signaling Identifiers
Both threat actors manipulated the signaling identifiers embedded within the attack messages to conceal the true origin of the traffic and influence the routing path of the responses. This process involved altering operator network Hostnames and domains, directly violating protocol standards and GSMA security guidelines.
2. Sequential Transaction Identifiers (TID) in SS7
Location queries utilized near-sequential Transaction Identifiers (TIDs) for surveillance messages across various SS7 networks. Under normal circumstances, TIDs are generated entirely independently by Network Elements within each operator’s network. The presence of sequential identifiers indicates that the signaling queries were generated by a centralized surveillance Command and Control (C2) platform.
3. Non-Standard Session IDs in Diameter
The Session ID values for both actors deviated from 3GPP Diameter standards, using the origin-host;timestamp;local-id format. However, each actor implemented this format differently:
- First Actor: Generated long, randomized numeric tokens (37 to 39 digits) resembling 128-bit identifiers (UUID style); a format frequently generated by C2 systems.
- Second Actor: Directly embedded the target’s IMSI identifier within the Session ID; this allowed the surveillance system to track and correlate responses associated with specific target devices.
4. Identical Commands Across Networks
The commands observed in the attack messages utilized exactly identical parameters across multiple different networks. The use of identical parameters in SS7 and Diameter protocols (as evident in the logs) clearly indicates that these messages were generated by a centralized system sending the exact same recurring queries.
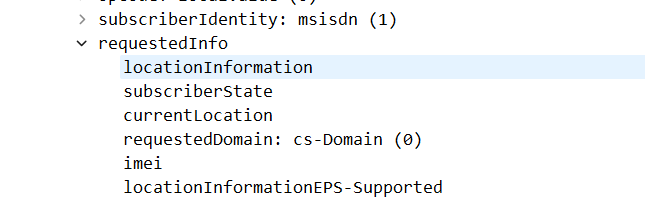
An overview of the commands utilized by the attacker is summarized in Table 5 below.
| Protocol | Command / Parameter | Description |
|---|---|---|
| SS7 | locationInformation |
Request for any available location data in the network, including Cell ID, Location Area Code (LAC), Mobile Country Code (MCC), and Mobile Network Code (MNC). |
| SS7 | subscriberState |
Request for the device’s current network state (e.g., roaming, busy, unreachable, or attached/reachable). |
| SS7 | currentLocation |
Request for the current serving Cell ID associated with the device. |
| SS7 | requestedDomain cs-Domain (0) |
Indicates that this query targets the Circuit-Switched service domain, which is used for voice and SMS services. |
| SS7 | imei |
Request for the device’s International Mobile Equipment Identity (IMEI). |
| SS7 | locationInformationEPS-Supported |
Request to check whether the network supports providing 4G location information. |
| Diameter | RAT-Type Requested |
Request for the Radio Access Technology type currently being used by the device (e.g., LTE, GSM, or UMTS). |
| Diameter | Local Time Zone Request |
Request for the time zone associated with the device’s current location. |
| Diameter | Current Location Request |
Request for 4G location data from the network, including Tracking Area Identity (TAI) and E-UTRAN Cell Global Identifier (ECGI). |
| Diameter | T-ADS Data Request |
Request for information used to determine how communications are managed (whether communications are handled via the IMS core or Circuit-Switched networks). |
Summary of identical parameters observed in the surveillance messages.
Gateways to Surveillance
Citizen Lab’s investigation in this report exposes three mobile networks that have repeatedly emerged as surveillance entry and transit points within the telecom ecosystem. These networks act as gateways, allowing traffic to traverse trusted signaling interconnections while simultaneously granting necessary access to the threat actors hiding behind their infrastructure.
019Mobile Operator (Israel)
019Mobile is a private mobile operator based in Israel operating under the brand name “Telzar 019”. The GSMA website indicates they began offering mobile services in 2013 and are “the sole provider of inbound and outbound roaming services at the Israel International Airport”. The researchers’ analysis shows that 019Mobile identifiers repeatedly appeared in Diameter surveillance attempts, both as the originating network and as an intermediary node. The Route-Record identifier indicates that 019Mobile Hosts acted as a First-hop Proxy for the traffic, positioning themselves as an entry and transit point for 4G location tracking. Citizen Lab also reveals that 019Mobile is hidden from DNS systems, whereas BGP routing records confirm its reachability via Partner Communications (one of Israel’s major telecommunications providers). Israel has long been a focal point for the global surveillance industry. Although Citizen Lab does not directly attribute the observed activities to 019Mobile, the role of this network—configured as a visible signaling intermediary, alongside Partner Communications as an invisible entry point into the global 4G signaling backbone—demonstrates how operator networks can be abused for international surveillance operations.
Airtel Jersey/Sure Operator (Channel Islands)
The Airtel Jersey operator (now part of the Sure Group) operates within the self-governing island of Jersey in the Channel Islands; a jurisdiction that has frequently been the subject of investigative reports regarding telecom surveillance and signaling abuse. In Citizen Lab’s investigation, an Airtel Jersey node was observed as the first hop for Diameter signaling surveillance queries (with activity dating back to 2022). The persistent use of telecommunications infrastructure from this jurisdiction suggests the existence of a reliable regulatory environment for telecom leasing activities.
Tango Networks UK Company
This company is a subsidiary of the US-based Tango Networks, which provides mobile services to enterprise customers. In 2022, the UK’s telecom regulator (Ofcom) assigned Mobile Network Code (MNC) 53, along with Mobile Country Code (MCC) 234, to this company. The organization’s investigations reveal a Diameter-based Hostname with a Tango Networks signaling identifier used as the second entry point for 4G location tracking queries by the first threat actor discussed in this report. Researchers verified the validity of this identifier in the attack via IPX DNS records and network details listed in IR.21, and noted the repeated, multi-year use of the company’s signaling identifiers in surveillance activities.
Altogether, these networks illustrate that in the modern world, “Access” is the core reality of telecom surveillance. Threat actors who secure agreements and integrate with legitimate operators to send queries into the global signaling system can route surveillance traffic on a massive scale.
STA1 Campaign: A Persistent Location Tracking Operation
In this investigation, researchers introduce the first threat actor as STA1; a persistent and technically sophisticated telecom surveillance group involved in long-term operations. Analysis indicates that STA1 possesses a deep understanding of mobile signaling protocols, the international roaming ecosystem, and signaling firewalls. This actor gains access to the private signaling backbone through multiple geographic entry points and employs a methodical approach to bypass network defenses.
Timeline of a Multi-Stage Location Tracking Campaign On November 25, 2024, a sequence of signaling messages from multiple foreign operator networks targeted a subscriber of a Middle Eastern mobile operator with the objective of location tracking. Following notification of the attack, the operator confirmed that the target’s IMSI belonged to a “VVIP” subscriber, indicating a high-value, top-tier surveillance target. The following activities demonstrate the tradecraft designed to bypass signaling firewall controls at the edge of the target network:
- Phase 1: Reconnaissance – 10:39 to 10:41 GMT
The attack initiates with the transmission of two SS7sendRoutingInfoForSM (SRISM)messages from a GT attributed to the SEATEL network in Cambodia. These messages attempted to extract the IMSI associated with the target user’s phone number; both attempts were blocked by the signaling firewall. - Phase 2: Initial Location Attempts via SS7 – 10:41 to 10:44 GMT
Actor STA1 immediately pivoted, sending multiple SS7provideSubscriberInfo (PSI)messages to probe the target network. In just three minutes, PSI requests were dispatched using GTs distributed across Cambodia, Mozambique, Sweden, Italy, Liechtenstein, and Uganda. This rapid rotation among multiple network sources was a clear tactic to find a Trusted Pathway through the firewall. - Phase 3: Protocol Switch to 4G/Diameter – 10:46 to 10:50 GMT
Following the failure of the SS7 attempts, the attacker switched to the Diameter protocol, sending sixInsert-Subscriber-Data-Request (IDR)messages from a Host in the UK (Tango Networks), followed by another 19 IDR messages from 019Mobile (Israel). This continuous shifting of protocol and originating network demonstrates the capability to adapt techniques to bypass the firewall. - Phase 4: Return to SS7 and Escalation – 10:56 to 11:20 GMT
After 25 unsuccessful Diameter attempts, the attacker reverted to the SS7 PSI method, utilizing the same previous GTs. Following an eight-minute pause, the attack escalated to another SS7 tactic: using a command calledanyTimeInterrogation (ATI), which is typically used for mobile location tracking. Twelve ATI messages were sent from the same GT cluster. - Phase 5: Final Diameter Manipulation Attempt – 13:29 to 14:27 GMT
After a two-hour hiatus, STA1 returned to Diameter with a new tactic. An IDR message was sent from a new operator Hostname associated with AIS Thailand. Even more suspicious was that theOrigin-Realmattribute utilized a network domain belonging to China Unicom. This spoofing was designed to route the location query through an alternative interconnect path.
Conclusion
Over a four-hour period, STA1 executed a coordinated sequence of location tracking attempts against a single user. The actor alternated between SS7 and Diameter protocols, rotating queries across 11 operator identities in 9 countries to masquerade as legitimate roaming traffic. This campaign involved complex manipulation of signaling identifiers and routing paths (including mismatched source Hosts and network realms for traffic steering).
| Time (GMT) | Protocol | Signaling Operation | Source Node | Country | Originating Network / Realm |
|---|---|---|---|---|---|
| 11/25/24 10:39 | SS7 | sendRoutingInfoForSM |
855183901014 | Cambodia | SEATEL |
| 11/25/24 10:41 | SS7 | sendRoutingInfoForSM |
855183901014 | Cambodia | SEATEL |
| 11/25/24 10:41 | SS7 | provideSubscriberInfo |
855180015170 | Cambodia | SEATEL |
| 11/25/24 10:41 | SS7 | provideSubscriberInfo |
25882200300 | Mozambique | TMCEL |
| 11/25/24 10:42 | SS7 | provideSubscriberInfo |
85513000755 | Cambodia | CADCOMMS (QB) |
| 11/25/24 10:42 | SS7 | provideSubscriberInfo |
46764753182 | Sweden | TELENABLER AB |
| 11/25/24 10:43 | SS7 | provideSubscriberInfo |
393358840745370 | Italy | TIM |
| 11/25/24 10:43 | SS7 | provideSubscriberInfo |
855183901014 | Cambodia | SEATEL |
| 11/25/24 10:43 | SS7 | provideSubscriberInfo |
423790105844 | Liechtenstein | FL1 |
| 11/25/24 10:43 | SS7 | provideSubscriberInfo |
855183901014 | Cambodia | SEATEL |
| 11/25/24 10:44 | SS7 | provideSubscriberInfo |
25671000036 | Uganda | UTEL |
| 11/25/24 10:46 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
| 11/25/24 10:47 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
| 11/25/24 10:47 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
| 11/25/24 10:47 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
| 11/25/24 10:47 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
| 11/25/24 10:47 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
| 11/25/24 10:48 | Diameter | Insert-Subscriber-Data-Request |
ideabpl1h.epc.mnc019.mcc425.3gppnetwork.org |
Israel | 019MOBILE |
| … | … | … | … | … | … |
| 11/25/24 10:59 | SS7 | provideSubscriberInfo |
25671000036 | Uganda | UTEL |
| 11/25/24 11:17 | SS7 | anyTimeInterrogation |
25882200300 | Mozambique | TMCEL |
| … | … | … | … | … | … |
| 11/25/24 11:20 | SS7 | anyTimeInterrogation |
85513000755 | Cambodia | CADCOMMS |
| 11/25/24 13:29 | Diameter | Insert-Subscriber-Data-Request |
ideabpl1h.dea.epc.mnc003.mcc520.3gppnetwork.org |
Thailand/China | AIS/CHINA UNICOM |
| 11/25/24 13:29 | Diameter | Insert-Subscriber-Data-Request |
ideabpl1h.epc.mnc019.mcc425.3gppnetwork.org |
Israel | 019MOBILE |
| 11/25/24 13:29 | Diameter | Insert-Subscriber-Data-Request |
ideabpl1h.epc.mnc019.mcc425.3gppnetwork.org |
Israel | 019MOBILE |
| 11/25/24 14:27 | Diameter | Insert-Subscriber-Data-Request |
cst001.epc.mnc053.mcc234.3gppnetwork.org |
UK | TANGO NETWORKS |
Attack sequence for STA1 on November 25, 2024.
Note: This table provides a summarized view of the attack sequence. The complete dataset includes an additional 17 IDR attempts from 019Mobile (between 10:49 and 10:50 GMT), along with further SS7 PSI and ATI activities from the same source nodes (Global Titles) shown above.
Concealment and Evasion via Diameter Manipulation
Executing telecom surveillance on a massive scale requires more than just access to the global signaling ecosystem; it also necessitates stealth to keep the origin of the attacks hidden. Actor STA1 achieved this by utilizing multiple SS7 and Diameter entry points while simultaneously rotating operator signaling identities to make the attack traffic appear as legitimate signaling traffic.
This concealment was notably evident in the Diameter message headers. The Origin-Host, Origin-Realm, and Route-Record fields identify the sending system and trace the path of a message across the interconnect network. Analysis of these fields revealed three distinct routing patterns designed to obscure the source of the queries and increase the likelihood of bypassing the signaling firewall:
- Direct access via Tango Networks UK: Messages entered the network through Tango-associated infrastructure and were routed via the BICS IPX network.
- Direct access via 019Mobile Israel: Surveillance traffic entered through nodes associated with the 019Mobile network before reaching IPX providers.
- Path with spoofed operator identity (AIS Thailand / China Unicom): Messages combined a Hostname belonging to operator AIS Thailand with a network domain (Realm) belonging to China Unicom, while simultaneously routing through 019Mobile to steer the attack traffic via Syniverse IPX.
Table 7 summarizes the key identifiers associated with these routing patterns:
| Originating Operator Identity | Origin-Host | Origin-Realm | First Hop Route-Record | Second Hop / IPX Provider |
|---|---|---|---|---|
| Tango Networks (UK) | cst001.epc.mnc053.mcc234 |
epc.mnc053.mcc234.3gppnetwork.org |
cst001.epc.mnc053.mcc234 |
dra01.epc.mnc053.mcc234(Hosted by BICS) |
| 019Mobile (Israel) | ideabpl1h.epc.mnc019.mcc425 |
epc.mnc019.mcc425.3gppnetwork.org |
vdrap1.epc.mnc019.mcc425 |
Comfone |
| AIS (Thailand) + China Unicom | ideabpl1h.dea.epc.mnc003.mcc520 |
epc.mnc001.mcc460.3gppnetwork.org |
vmdra01.epc.mnc019.mcc425 |
Syniverse |
Signaling identifiers and routing paths related to STA1 location tracking in Diameter.
As previously shown in Table 3, the interconnect providers observed relaying SS7 traffic from operator GTs did not always correspond to what was reported in the registered IR.21 documents. By distributing the surveillance operation across multiple identities and utilizing indirect third-party signaling paths, the threat actor was able to send their surveillance queries with reduced detection exposure while simultaneously increasing the chances of a breach into the target network.
Figure 5 illustrates how STA1 sent surveillance messages into the global signaling ecosystem using multiple operator identities and interconnect routing paths.
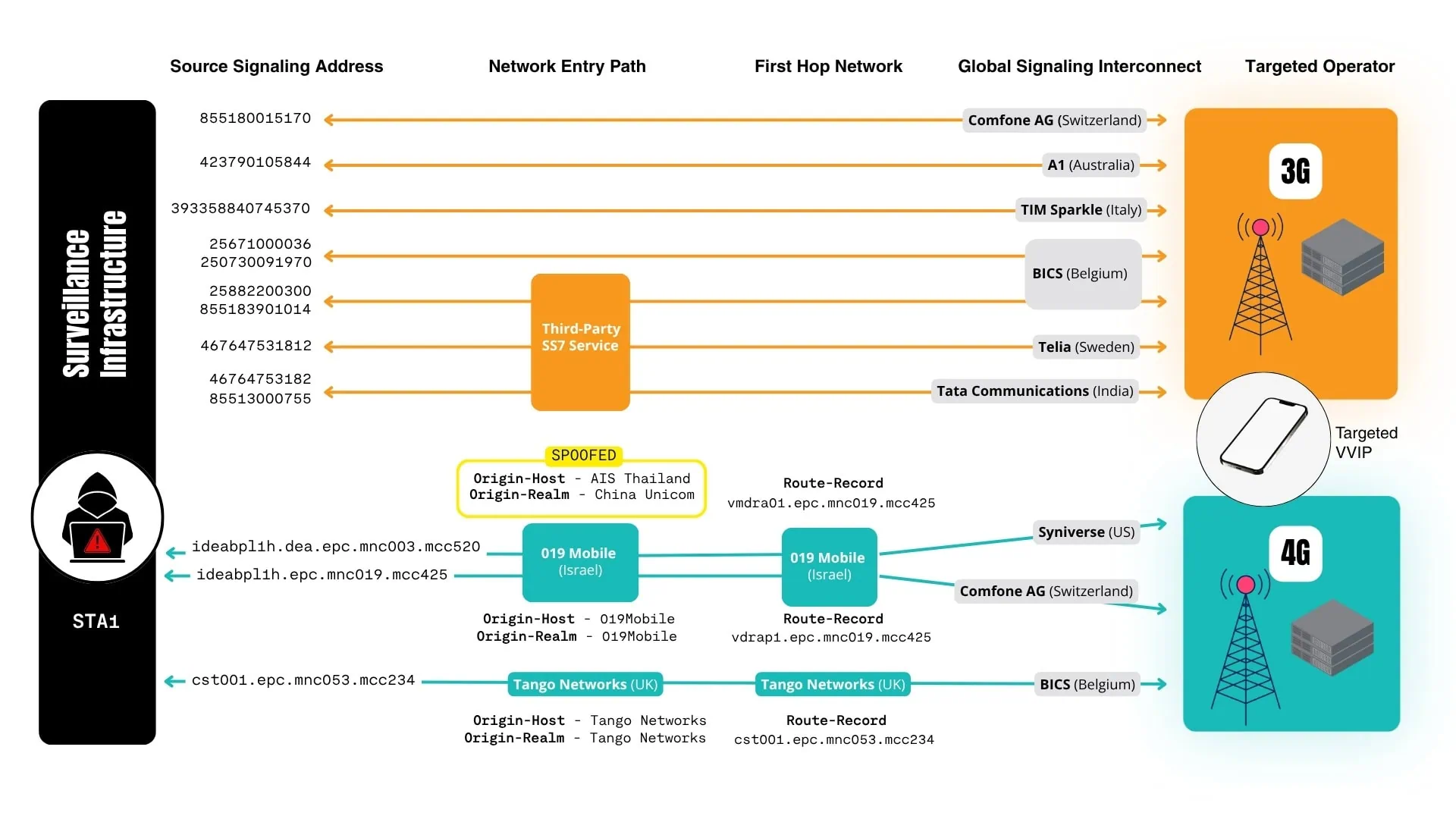
Figure 5 displays the routing paths used in the STA1 campaign across 3G (SS7) and 4G (Diameter) networks. In the 3G section (top), GTs from multiple operators were used to route surveillance traffic through different entry points into the network, creating diverse paths within the signaling backbone. In the 4G section (bottom), the actor utilized the UK’s Tango Networks to send traffic to the BICS IPX network, and Hostnames from 019Mobile to send messages to Comfone IPX. Ultimately, the identities of AIS Thailand and China Unicom networks were spoofed to send messages through Syniverse IPX.
This pattern indicates a centralized surveillance Command and Control (C2) platform deeply integrated into the signaling ecosystem, providing multiple routing options for covert and stealthy access to target networks worldwide.
Operational Techniques and Tradecraft
1. Route-Record Manipulation (Tango Networks UK)
- What is observed: An
Origin-Hostbelonging to Tango Networks (with the addresscst001.epc.mnc053.mcc234.3gppnetwork.org) is duplicated inRoute-Record 1. - Why it is anomalous: According to the IETF Diameter protocol standard (RFC 6733), any relay that forwards a request must append its identity to the
Route-Record. TheOrigin-Hostfield identifies the sending node and should not appear as a relay in the path unless the node is forwarding a message through itself. - Impact: This manipulation conceals the First Hop in the network path as well as the routing of response messages, allowing the attacker to keep the network paths toward the target network and from its origin hidden.
2. Origin-Host (Thailand) and Origin-Realm (China) Mismatch
- What is observed: A Diameter message using the
Origin-Hostof operator AIS Thailand is paired with a network domain (Origin-Realm) belonging to China Unicom to route traffic through the Syniverse IPX network and deliver the message along the interconnection path. - Why it is anomalous: The
Origin-Hostattribute specifies the Hostname/client sending the message, whereas theOrigin-Realmidentifies the network to which the message belongs. Together, these form the Diameter signaling identity; they are crucial for the receiving operator to identify the message owner and must strictly belong to the same network. Pairing information from different operators violates GSMA and 3GPP standards, indicating identity spoofing and manipulation. - Impact: This mismatch conceals the message’s point of origin in an attempt to find a Trusted Path through the firewall into the target network.
3. Use of an Israeli Network for Interconnecting Thailand/China Network Traffic
- What is observed: A node belonging to Israel’s 019Mobile (with the address
vmdra01.epc.mnc019.mcc425.3gppnetwork.org) acts as the First Hop for an attack message originating from AIS Thailand/China Unicom networks. - Why it is anomalous: According to IR.21 documents, neither AIS nor China Unicom has any IPX agreement with Israel’s 019Mobile to relay signaling traffic between other foreign operators.
- Impact: Actor STA1 is configuring 019Mobile as an alternative routing path to relay 4G surveillance traffic.
4. Standard Workarounds for Location Queries
- What is observed: Since STA1’s attempts to obtain the target phone’s IMSI were blocked, they manipulated the parameters of the Diameter and SS7 messages as a workaround.
- Why it is anomalous: SS7 PSI and Diameter IDR queries are typically keyed on the phone’s IMSI. Using only the MSISDN (phone number) to query the network is non-standard.
- Impact: This technique facilitates surveillance operations by provoking and receiving responses from operators with weak firewall controls.
Weak Links in the Global Interconnect Chain
Operators 019Mobile (Israel) and Tango Networks (UK) as Proxy Nodes: Actor STA1 utilized both operators as entry and exit points in the routing path of the 4G attacks. The use of different 019Mobile Hostnames from separate originating networks indicates deliberate Traffic Steering:
- Identity originating from 019Mobile: First Proxy (
vdrap1.epc.mnc019.mcc425.3gppnetwork.org) - Identity associated with AIS/China: Second Proxy (
vmdra01.epc.mnc019.mcc425.3gppnetwork.org)
This pattern shows that STA1 used 019Mobile as a proxy to deliver location queries while keeping the origin of its C2 infrastructure hidden.
Failure in IPX Traffic Screening:
The Syniverse IPX network allowed a signaling message with a Host belonging to AIS and a network domain from China Unicom to transit their IPX network prior to delivery to the target operator:
- As interconnect hubs for global operators, IPX providers are expected to screen sender messages and block/reject those using mismatched network identifiers.
- In this case, Syniverse failed to adhere to protocols, and a surveillance message passed through unchecked, imposing severe vulnerability risks on the target operator.
Strategic Use of IPX Providers:
Actor STA1 utilized specific IPX routing paths identified by the Hostname observed in the Route-Record field of the message:
- Injecting an operator Hostname in the
Route-Recordfield influences the routing path while simultaneously obscuring the original sender of the signaling traffic. - Influencing the transit path of messages provides more opportunities to reach the target network and breach the signaling firewall.
Attribution Assessment
Attributing a telecom surveillance operation to a specific group is inherently challenging. The use of legitimate operator identifiers and signaling access through leasing agreements or third parties provides a layer of Operational Concealment. Consequently, this investigation does not directly attribute the activity to a specific government or organization. Instead, the available indicators were examined to evaluate the most probable operational model and actor type.
Although the technical patterns align with the operation of a Commercial Surveillance Vendor (CSV)—which uses a centralized, cloud-based C2 platform to serve multiple clients—Citizen Lab researchers analyzed operator information and routing metadata through collaboration with mobile industry partners.
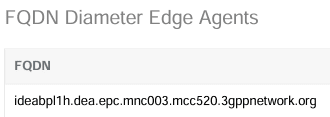
1. Use of AIS Thailand Formats and an IR.21-Registered Node: The surveillance activity associated with 019Mobile consistently used the Hostname format of the AIS Thailand company (i.e., ideabpl1h). In the most sophisticated tracking attempt, STA1 configured a Diameter Edge Agent (DEA) node belonging to AIS Thailand (corresponding to Figure 6 of the report)—a node typically used for inter-operator routing and topology hiding—while setting the Origin-Realm to belong to China Unicom.
This combination indicates deep, granular knowledge of operator infrastructure, interconnection relationships, and access to GSMA IR.21 data. Such capabilities are uniquely consistent with a Sophisticated Commercial Telecom Surveillance Operation.
2. Repeated Campaign Activity:
Another surveillance campaign, shown in Figure 7 and captured by Cellusys in March 2025, reveals multiple attempts at location tracking. In these attempts, an Origin-Host belonging to China Unicom (with the address dex01.epc.mnc001.mcc460.3gppnetwork.org) was spoofed, using the exact same Route-Record belonging to Israel’s 019Mobile that was previously observed in the November 2024 attack.
![]()
3. Long-Running Campaign Activity:
Historical Telemetry indicates a long-running activity utilizing the same Hostname formats and identifiers belonging to multiple operators, dating back to at least November 2022 (as shown in Table 8). The use of similar Hostnames associated with multiple network operators over extended periods aligns with Address Spoofing patterns designed to conceal the attack’s origin. Telemetry data shows these Hostnames were used in over 500 location tracking attempts.
| Date | Origin Host Address | Operator | Origin Host Country | Threat Type | Operation |
|---|---|---|---|---|---|
| November 9, 2022 | dex01.epc.mnc002.mcc228... |
SUNRISE SWITZERLAND | Switzerland | Location Discovery | Insert-Subscriber-Data-Request |
| November 9, 2022 | dex01.epc.mnc001.mcc712... |
KOLBI COSTA RICA | Costa Rica | Location Discovery | Insert-Subscriber-Data-Request |
| November 9, 2022 | dex01.epc.mnc001.mcc260... |
PLUS POLAND | Poland | Location Discovery | Insert-Subscriber-Data-Request |
| March 1, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| March 2, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| March 22, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| March 30, 2023 | dex01.epc.mnc019.mcc425... |
019MOBILE | Israel | Location Discovery | Insert-Subscriber-Data-Request |
| March 30, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| August 30, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| September 18, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| September 20, 2023 | dex01.epc.mnc019.mcc425... |
019MOBILE | Israel | Location Discovery | Insert-Subscriber-Data-Request |
| September 20, 2023 | dex01.epc.mnc001.mcc460... |
CHINA UNICOM | China | Location Discovery | Insert-Subscriber-Data-Request |
| September 26, 2023 | dex01.epc.mnc019.mcc425... |
019MOBILE | Israel | Location Discovery | Insert-Subscriber-Data-Request |
| September 26, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| September 26, 2023 | dex01.epc.mnc019.mcc425... |
019MOBILE | Israel | Communications Interception | Authentication-Information-Request |
| September 26, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Communications Interception | Authentication-Information-Request |
| September 27, 2023 | dex01.epc.mnc019.mcc425... |
019MOBILE | Israel | Location Discovery | Insert-Subscriber-Data-Request |
| September 27, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| December 10, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK | UK | Location Discovery | Insert-Subscriber-Data-Request |
| December 10, 2023 | dex01.epc.mnc019.mcc425... |
019MOBILE | Israel | Location Discovery | Insert-Subscriber-Data-Request |
| December 11, 2023 | dex01.epc.mnc001.mcc460... |
CHINA UNICOM MOBILE | China | Location Discovery | Insert-Subscriber-Data-Request |
| December 14, 2023 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK LTD | UK | Location Discovery | Insert-Subscriber-Data-Request |
| January 8, 2024 | cst001.epc.mnc053.mcc234... |
TANGO NETWORKS UK LTD | UK | Location Discovery | Insert-Subscriber-Data-Request |
| January 8, 2024 | dex01.epc.mnc006.mcc454... |
SMARTONE | Hong Kong | Location Discovery | Insert-Subscriber-Data-Request |
STA1 attack history.
Note: This table displays only a limited sample of historical attacks from over 500 recorded threat events attributed to STA1 since November 2022. (Due to the length of the domain names, the term .3gppnetwork.org has been abbreviated in the table).
4. Global Targeting Patterns
Beyond the initial targeting of a high-profile user in the Middle East, we identified surveillance activities across a vast geographic expanse. Targets included individual mobile subscribers associated with operators in Thailand, South Africa, Norway, Bangladesh, Denmark, Sweden, Malaysia, Montenegro, and several countries throughout the Sub-Saharan Africa region.
Targeting a single user across multiple operator networks and jurisdictions over years is a hallmark of a commercial surveillance platform deployed across multiple operators and likely utilized by multiple global clients.
5. DNS Validation for Operator-Controlled Signaling Infrastructure
Researchers analyzed IPX DNS records to determine the Authoritative operators associated with the domains observed in the attack traffic. The Tango Networks Hostname cst001.epc.mnc053.mcc234.3gppnetwork.org successfully resolved via authoritative IPX DNS, confirming this address is a valid, operator-controlled Hostname consistent with Tango Networks’ IR.21 records. Its repeated use in surveillance activities indicates STA1 has had long-term access to Tango Networks’ infrastructure (likely through a commercial agreement).
However, the analysis of 019Mobile yielded different results. The domain epc.mnc019.mcc425.3gppnetwork.org consistently returned NXDOMAIN (meaning domain does not exist) responses across multiple IPX DNS servers. This suggests the domain either did not exist or was intentionally Suppressed from the root environment of the IPX DNS system. This points to a potential technique to hide the discovery of IP addresses belonging to 019Mobile—attributed to the signaling Hosts transmitting the surveillance traffic. The research team sought further network data to investigate whether 019Mobile’s infrastructure was Reachable via Diameter signaling.
In the absence of a successful DNS resolution, they checked whether any IP networks belonging to 019Mobile were advertised within the IPX network. They found that two IP address ranges and their corresponding Autonomous System Number (ASN 51825) were listed in the registered IR.21 documents belonging to the Israel-based operator Partner Communications.
GRX/IPX Routing for Data Roaming
Connection to IPv4 Intercarrier Backbone (Inter-PMN)
| IP Address (Range) | VLAN in IPX | Network Owner |
| 185.24.204.0/29 | Data-Roaming | MNO |
| 185.24.204.8/29 | Data-Roaming | MNO |
Autonomous System Numbers (ASN)
| ASN | Network Owner |
| 51825 | MNO |
The ASN 51825 identifier is a unique network ID registered to “Telzar 019 International Telecommunications Services LTD” (the parent company of 019Mobile); a point also illustrated in Figure 8.
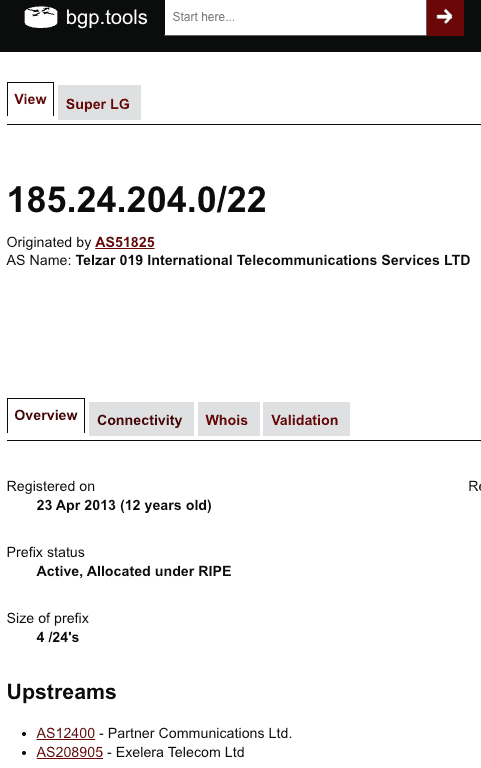
This registered association in IR.21 indicates that Partner Communications acts as the Upstream signaling interconnect provider for 019Mobile. This, however, raises a critical question: if 019Mobile’s network domain does not exist within the IPX (the NXDOMAIN response in DNS resolution), is its Underlying infrastructure still Reachable in the signaling ecosystem?
To validate this, researchers analyzed BGP routing information obtained from within the IPX backbone. The results confirmed that the IP address Prefixes belonging to 019Mobile are actively being Advertised and are accessible via Partner Communications; indicating a verifiable routing path into and out of the Diameter signaling ecosystem. The BGP routing path was as follows:
AS Path: → 12400 → 51825
This path shows that signaling traffic destined for 019Mobile (with ASN 51825) is routed through an Intermediary network belonging to Partner Communications (with ASN 12400) before reaching its destination. The presence of the Partner network in this routing path confirms that 019Mobile’s infrastructure is accessible through an established and defined interconnect relationship. Additional routing Attributes indicate that this Valid route was Externally learned and selected as the Best route in the routing table:
Origin: IGP | localpref: 100 | valid, external, best
These findings confirm that despite the absence of the 019Mobile domain in Authoritative IPX DNS records, surveillance traffic entering and exiting through this network can be successfully routed and Delivered, while remaining Hidden from DNS discovery. Although researchers do not believe 019Mobile itself conducted these attacks, the evidence suggests that its network, as well as Partner Communications, were likely abused as a transit path for surveillance traffic.
The findings detailed above provide deep insight into the methods utilized by STA1 to operate within the global signaling ecosystem (while limiting the possibility of Attribution). In both SS7 and Diameter protocols, Routing Manipulation, Path Obfuscation, and signaling identifiers associated with multiple different operators have been used to deliver surveillance traffic. These approaches, employed over several years, demonstrate a high degree of Persistence, Sophistication, and Coordination. The global distribution of targets and infrastructure suggests a system designed for Multiple Tenants, aligning perfectly with a commercially developed telecom surveillance platform that supports government intelligence activities. While it is currently not possible to attribute this campaign to a specific actor, the evidence clearly points to a calculated, well-funded operation deeply integrated into the mobile signaling ecosystem.
STA2 Campaign: The SIM as the Spy
The second investigation, attributed to a group dubbed Surveillance Threat Actor 2 (STA2), utilized different techniques in the realm of mobile surveillance. Instead of merely manipulating SS7 and Diameter signaling protocols for location tracking, STA2 combined Device-level Exploitation with Network-level attacks.
Through detailed log analysis and examining SMS Header content in a Packet Trace, researchers discovered that STA2 sent a specially formatted Binary SMS containing Embedded Commands. This was observed in the attack sequence described in this section.
This SMS was designed to silently trigger a SIM-based Exploit without requiring any user interaction (Zero-Click), along with commands that turned the target phone into a location tracking device. The research team linked this Binary Payload to a long-running campaign likely affecting thousands of devices, known as SIMjacker.
The SIMjacker vulnerability (initially disclosed by ENEA in 2019) is a Zero-Click SMS exploit that invokes a hidden application on the SIM card called the S@T browser. The S@T browser is a SIM toolkit (STK) application that interprets S@T Bytecode and provides access to STK commands. STK applications are typically used by mobile operators for Service Provisioning, operator phone configurations, and other value-added services. In this instance, STA2 sent a command instructing the STK to obtain the device’s location and return it via a silent SMS to attacker-controlled infrastructure.
At the time of this vulnerability’s disclosure, ENEA stated that SIMjacker was “currently being actively used by a specific private company that works with governments to monitor individuals.” Although ENEA did not name this company, Citizen Lab linked the sources of these attacks to SS7 addresses belonging to mobile operators based in Rwanda, Sweden, and Liechtenstein. This attack is effectively a continuation of the SIMjacker threat, wherein the user’s SIM card is essentially turned into a sensor and Spy, using SMS to communicate with Command and Control (C2) servers.
How can an SMS control a phone’s SIM card?
SIM toolkit messages (also known as SIM OTA messages) look nothing like standard text messages; your phone never displays them, and users have no way of knowing they were received, as these messages are used by network operators to configure device network settings. Two fields within the SMS Header make this possible:
1. Value TP-PID = 127 – (This message is for the SIM card, not the user) Attackers use this field to instruct the device to do the following:
- Do not display the message
- Do not save it in the Inbox
- Deliver it directly to the SIM card for Execution
2. Value TP-DCS = 22 (0x16) – (Treat this as binary code and send it directly to the SIM card) This field ensures that the Malicious Code embedded in the SMS is identifiable and the commands are executed by the SIM card:
- The message contains binary commands
- The instructions must be processed by the device’s SIM card
- The device’s messaging app must not access (or touch) the message content
A Different Modus Operandi
The footprints and Signatures of the STA2 group are vastly different from STA1. On February 11, 2025, the STA2 group attempted to execute a location tracking operation using a Sequential Approach, combining network and device attack vectors. The attack initiated with initial reconnaissance over SS7 and location tracking attempts, escalated to a SIM Exploit, and concluded with Diameter location tracking queries. The messages evaluated in this analysis (described in the attack sequence below) were captured, Flagged, and blocked by the signaling firewall detailed in Table 9.
Phase 1 – Probing over SS7 (15:41 GMT)
The attack began with a single SS7 PSI message from the GT numbered 467647531812. This message was likely used to Probe the target network to check whether it processes an initial location tracking request, as well as to verify if the target phone was connected to the network.
Phase 2 – Weaponizing SMS (15:45 GMT)
A few minutes later, the same GT sent an SS7 mt-ForwardSM (Mobile-Terminated Forward Short Message) message carrying a Binary Payload. This is the exact message that delivered the SIM Exploit.
Phase 3 – Cross-Protocol Camouflage (15:46 to 15:50 GMT)
After the SIM exploit was blocked, the attacker switched to Diameter and launched a series of Authentication-Information-Request (AIR) probe messages, followed by IDR location queries.
-
Network Probing using Fake Registration: The attacker sent 10 AIR messages containing the target phone’s IMSI using 5 different operator network identifiers. These messages were configured with an invalid
Visited-PLMN Id = 0000value. The AIR message is typically used to establish a new connection on the phone and report the roaming Mobile Country Code (MCC) and Mobile Network Code (MNC) values in theVisited-PLMN IDfield. However, in this case, the attacker was not attempting to connect; rather, they used a Malformed PLMN value to probe the target network’s security and lay the groundwork for receiving a successful response in subsequent location tracking attempts. - Follow-on Location Tracking: The attacker then sent a series of IDR location queries using network identifiers from 3 different countries. In each Diameter IDR message, the corresponding Flag was set to retrieve the current network status and location (Cell ID) of the target phone.
- Hostname and Routing Path Manipulation: The attacker used a single, Fixed Host in the
Route-Recordfield to steer the surveillance traffic toward the operator’s egress path, utilizing 2 different Hostname formats to identify the type of commands used in the attack. - Spoofed Networks: The Diameter messages utilized network identifiers originating from Poland (Plus), Switzerland (Sunrise), Morocco (INWI), Lesotho (Econet), Namibia (MTC), and Mozambique (Movitel). This indicates the attacker’s abuse of international signaling identities belonging to multiple operators.
| Time | Protocol | Signaling Operation | Source Node | Source Network | Origin Country | Threat Type |
|---|---|---|---|---|---|---|
| 2/11/25 15:41:33 | SS7 | begin, provideSubscriberInfo |
467647531812 | TELE2 | Sweden | Location Tracking |
| 2/11/25 15:45:29 | SS7 | begin, mt-ForwardSM |
467647531812 | TELE2 | Sweden | Binary SMS |
| 2/11/25 15:55:01 | Diameter | Authentication-Information-Request |
hss1.epc.mnc001.mcc260... |
PLUS | Poland | Malformed Message |
| 2/11/25 15:55:06 | Diameter | Authentication-Information-Request |
hss1.epc.mnc001.mcc260... |
PLUS | Poland | Malformed Message |
| 2/11/25 15:55:28 | Diameter | Authentication-Information-Request |
hss1.epc.mnc002.mcc228... |
SUNRISE | Switzerland | Malformed Message |
| 2/11/25 15:55:33 | Diameter | Authentication-Information-Request |
hss1.epc.mnc002.mcc228... |
SUNRISE | Switzerland | Malformed Message |
| 2/11/25 15:55:50 | Diameter | Authentication-Information-Request |
hss1.epc.mnc002.mcc604... |
INWI | Morocco | Malformed Message |
| 2/11/25 15:55:50 | Diameter | Authentication-Information-Request |
hss1.epc.mnc002.mcc604... |
INWI | Morocco | Malformed Message |
| 2/11/25 16:05:24 | Diameter | Authentication-Information-Request |
hss1.epc.mnc002.mcc651... |
ECONET | Lesotho | Malformed Message |
| 2/11/25 16:05:28 | Diameter | Authentication-Information-Request |
hss1.epc.mnc002.mcc651... |
ECONET | Lesotho | Malformed Message |
| 2/11/25 16:05:36 | Diameter | Authentication-Information-Request |
hss1.epc.mnc001.mcc649... |
MTC | Namibia | Malformed Message |
| 2/11/25 16:05:41 | Diameter | Authentication-Information-Request |
hss1.epc.mnc001.mcc649... |
MTC | Namibia | Malformed Message |
| 2/11/25 16:06:37 | Diameter | Insert-Subscriber-Data-Request |
hss.epc.mnc002.mcc651... |
ECONET | Lesotho | Location Discovery |
| 2/11/25 16:06:43 | Diameter | Insert-Subscriber-Data-Request |
hss.epc.mnc002.mcc651... |
ECONET | Lesotho | Location Discovery |
| … | … | … | … | … | … | … |
| 2/11/25 16:07:31 | Diameter | Insert-Subscriber-Data-Request |
hss.epc.mnc001.mcc649... |
MTC | Namibia | Location Discovery |
| 2/11/25 16:07:36 | Diameter | Insert-Subscriber-Data-Request |
hss.epc.mnc001.mcc649... |
MTC | Namibia | Location Discovery |
| … | … | … | … | … | … | … |
| 2/11/25 16:12:32 | Diameter | Insert-Subscriber-Data-Request |
hss.epc.mnc003.mcc643... |
MOVITEL | Mozambique | Location Discovery |
| 2/11/25 16:12:37 | Diameter | Insert-Subscriber-Data-Request |
hss.epc.mnc003.mcc643... |
MOVITEL | Mozambique | Location Discovery |
Attack sequence for STA2 (February 11, 2025).
Note: This table is abridged for brevity. Ten additional IDR attempts from ECONET, MTC, and MOVITEL networks are fully detailed in the log data.
Technical Fingerprints
The STA2 group utilized several recurring indicators that assisted researchers in categorizing and Clustering related activities over time:
1. Embedding IMSI in the Diameter Session-ID field
The target device’s IMSI identifier was Hardcoded in the Session-ID field. This signature directly links the attack messages to the target and indicates the use of custom tools with poor Operational Security (OPSEC). This signature was observed in both this attack and subsequent attacks that continued from 2025 into early 2026.
2. Hostname Naming Conventions for Labeling the Command Code Field in Diameter
Hostname formats indicated what type of signaling message was sent. This naming convention reveals that the Hostnames were actually used as Internal Labels to differentiate the surveillance queries:
hss1Hostnames were used for AIR probe messages.hssHostnames were used for IDR location queries.
3. Fixed Entry Path via the Jersey-Airtel Network
All attacks utilized exactly one fixed Host in the Route-Record field: dra1.je211.epc.mnc003.mcc234.3gppnetwork.org. The repeated use of this identical Host indicates that STA2 used a single operator network to route surveillance traffic into the IPX backbone.
Deconstructing the Binary SMS: Inside an Over-The-Air (OTA) SIMjacker Exploit
Historically, malicious actors have always used hidden commands within specific types of SMS messages. The Deconstruction of the binary SMS sent by STA2 provided unique insights into this surveillance operation.
A Packet Capture and logs obtained from the signaling firewall revealed the Headers of this SMS and accurately confirmed the message Timestamps. Analyzing how the attack was deployed and the informational elements defined in the structure of this SMS (shown in Figure 9 of the main report) reveals the precise operation of this covert exploit.
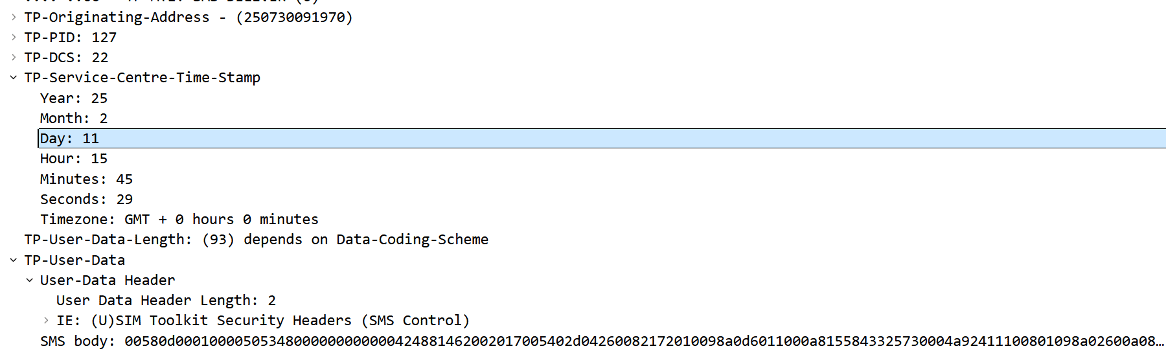
Analysis of the Attack SMS Details:
- SMS Source Address (TP-Originating Address or TP-OA):
250730091970– Identifies the SMS sender’s phone number, configured by the attacker and belonging to Airtel Rwanda. - Protocol Identifier (TP-Protocol Identifier or TP-PID):
127– Specifies that this message is intended for use by a SIM card application. - Data Coding Scheme (TP-Data Coding Scheme or TP-DCS):
22– Indicates that the message is binary; thus, the message is not processed like a standard text SMS.
The TP-PID and TP-DCS values indicate a SIM toolkit message containing instructions for the SIM card. This type of SMS is invisible to the user and is automatically Parsed by the SIM card without any user interaction.
- User Data (TP-User-Data): This field contains the main Body of the SMS.
SIMjacker attacks exploit a hidden application on the SIM card called the S@T browser (which is part of the SIM toolkit or STK). This exploit allows the attacker to Hijack the SIM card invisibly and without user interaction. To execute this attack, STA2 sent an SMS containing Bytecode that included specialized commands for the S@T browser (referencing Figure 10 of the report).
The S@T browser interprets and executes these commands immediately because this communication lacks an Authentication process. Consequently, the attacker does not need to send additional messages to authenticate themselves before the S@T browser is ready to receive commands. Researchers found that the binary SMS blocked by the firewall clearly matched the structure of S@T browser commands. This SMS uses a standard format to encode commands and their parameters (according to S@T bytecode specifications). The correct structure of the bytecode used by the attacker confirms that this message was used as a SIM-level exploit, not as standard SMS traffic.
What is the TL[A]V Format?
Data structures in the Tag-Length-[Attribute]-Value or TL[A]V format consist of four fields: Tag, Length, Attributes, and Value, where the Attributes field is optional.
S@T browser commands use the TL[A]V format, therefore:
- Each command is identified by a unique, one-byte Tag.
- The Tag indicates whether the Attribute field is present or not.
- The Length field specifies how many of the subsequent bytes are part of this command (this value includes the Attributes and Value fields).
- The Attributes field determines the specific parameters for that command.
- The Value field contains the data the command operates upon.
For example, the Init Variable command consists of a Tag with the value 0x20, followed by the Length and Value fields. The Value field contains the ID and the content of the initialized variable.
Payload and Message Header Details: The exploit SMS Payload includes a Command Header with the notable byte sequence 0x505348. This byte sequence represents the Toolkit Application Reference (TAR) value, which indicates a Low priority push message. Low priority push messages are designed for low-importance messages that do not require a Reply or delivery confirmation. As such, the messages leave no trace on the SIM card; if the S@T browser is busy when they arrive, these messages are simply Dropped. The reception and processing of these messages are completely Silent, so users are unable to notice them.
These messages offer an ideal Attack Surface because they bypass the Session creation process. This allows the attack message to be accepted immediately, eliminating the need to send prior messages to bring the target application to a Reception state.
Furthermore, the Security Parameter Indicator (SPI) in the header is 0x0001; this indicates that no Redundancy check, Cryptographic checksum, or digital signature was used in the message, and it merely requested a Proof of reception to be sent to the sender.
A Malicious Deck of Cards
A command Packet for the S@T browser is organized into structures called Decks, each containing Cards that group related commands. Since a packet can contain multiple Decks, the message payload begins with a Deck List that defines its structure.
The attack SMS included one Dynamic Deck along with one Card. The S@T browser never stores dynamic decks, so no trace of the attack remains on the SIM card. This makes Post-incident detection highly challenging. Only timestamped network traces can provide clues in this regard.
The card contained within the attack SMS encompasses five Commands. Each bytecode command is identified by a Tag. In addition to bytecode commands, the S@T browser is also capable of executing STK commands, which are sent from the SIM card to the phone as Proactive Commands. The phone’s Response is stored in one of the S@T browser’s variables.
Had the firewall not blocked this SMS, the following commands would have been executed sequentially by the S@T browser:
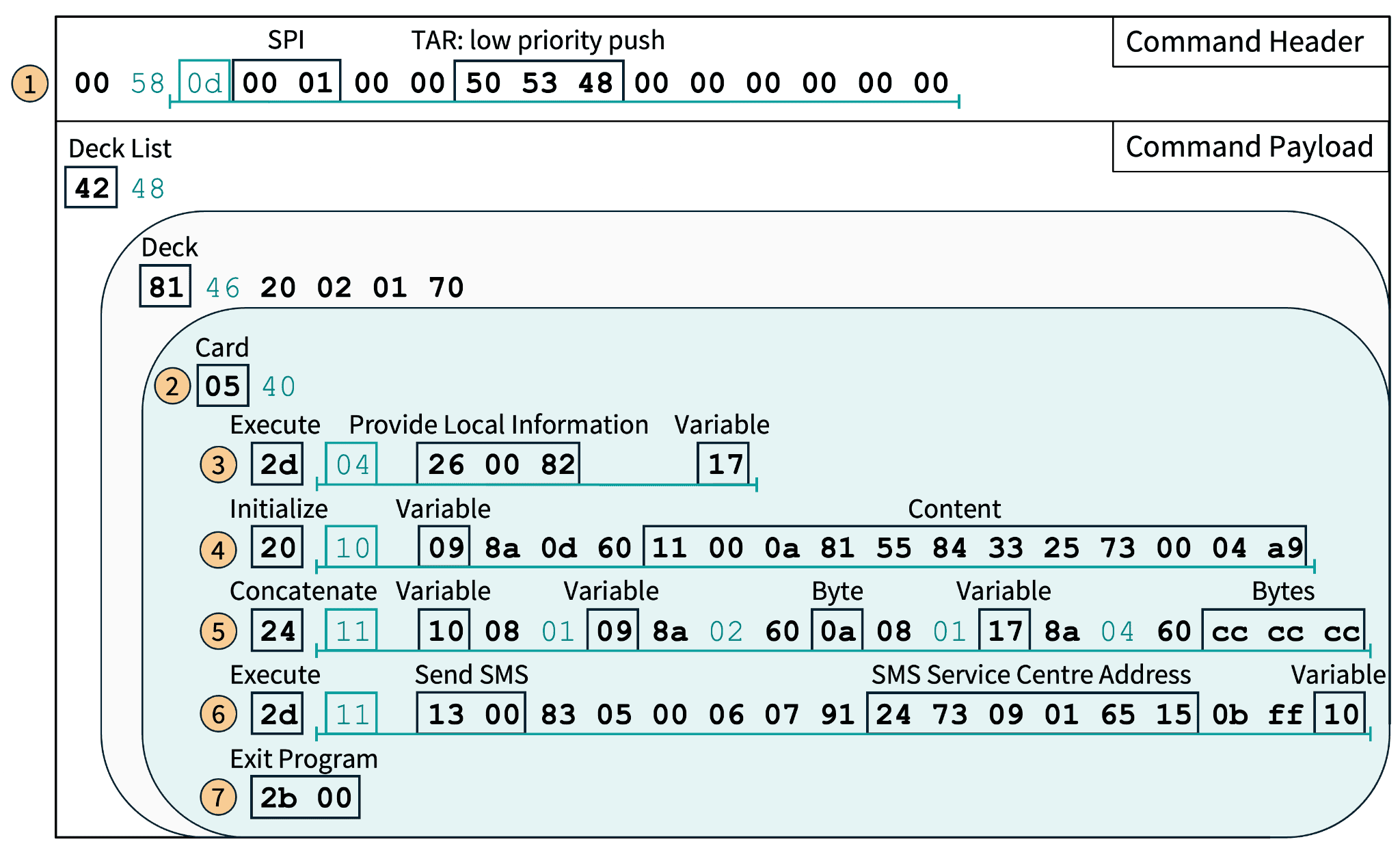
STK Command for Provide Local Information – Step (3): The first STK command instructs the S@T browser to send a Proactive Command to the phone, requesting information about the network cell the phone is currently connected to; namely, the Cell ID, Location Area Code (LAC), Mobile Network Code (MNC), and Mobile Country Code (MCC). The location information returned by the phone is stored in variable 0x17. Based on this data, the phone’s position can be determined with variable accuracy (from one kilometer in urban areas to a hundred kilometers in rural areas) depending on network cell density.
Initialize Variable – Step (4): Next, variable 0x09 is Initialized with 12 bytes of binary data. The content of these bytes is analyzed in the following section.
Concatenate Values – Step (5): In the next step, variable 0x09 is Concatenated with byte 0x0a, variable 0x17, and the byte sequence 0xcc 0xcc 0xcc. The result of this concatenation is stored in variable 0x10. This command effectively appends the location information stored in variable 0x17 to the binary data in variable 0x09, while simultaneously adding other padding bytes to this Stream.
STK Command to Send Short Message – Step (6): Finally, the S@T browser issues a proactive command to the phone to send an Exfiltration SMS containing the contents of variable 0x10. The destination address of this SMS is 423790105651, which is assigned to the FL1 operator in Liechtenstein. The parameters of this SMS are configured so that if the message fails to send, no Notification is displayed to the user to prevent discovery of the attack. The destination address of this outgoing SMS effectively reveals the network controlled by the attacker, as attackers require access to that network to receive the SMS.
Exit Program – Step (7): The last command exits the browser from the application.
The Exfiltration SMS
Because the attack SMS was blocked, it never reached the target phone, and consequently, no outgoing SMS containing location data was ever sent. However, by Parsing and decoding the commands Embedded within the intercepted SMS Payload, researchers reconstructed how the outgoing SMS would have been generated and exactly what information it would have contained had the attack been successful.
The research team analyzed the sequence of commands intended for execution by the SIM card (which defined how location data would be gathered and sent to the attacker). This exploit would have gathered its current location completely silently and transmitted it via SMS to the Short Message Service Center (SMSC) address configured by the attacker; all without any user interaction or visible indication on the device.
1. The SMS Header
The outgoing SMS is first constructed from the contents of variable 0x10 (see step 5 in Figure 10). The first 12 bytes of this variable contain binary data derived from variable 0x09 (step 4 in Figure 10). This data forms the SMS-SUBMIT header, which controls the type of SMS sent and how it is handled. In this specific case, the header specifies that the SMS is sent from a device to a remote SMSC, that it should accept Duplicates, and that no Delivery Confirmation is requested.
2. The SMS Destination
The subsequent bytes of variable 0x09 are populated with the destination user’s phone number, represented as 5548335237. This resembles a number in Brazil (with the +55 country code) but is incomplete and does not conform to valid country numbering formats. For this reason, it is unlikely to be used for routing or message delivery. Instead, this number likely serves as a Campaign Identifier within the STA2 surveillance infrastructure.
However, researchers were able to confirm that the configured SMSC address for this SMS matched a GT address observed in previous location tracking attacks. Based on this information, they assess with moderate confidence that this SMSC number was deliberately configured as a Command and Control (C2) endpoint by the STA2 group to route and collect the SMS payload containing the target device’s location data. Even though the ultimate destination number is invalid, attackers can access a message delivered to the SMSC address, thereby obtaining the exfiltrated location data without relying on delivery to an End-device.
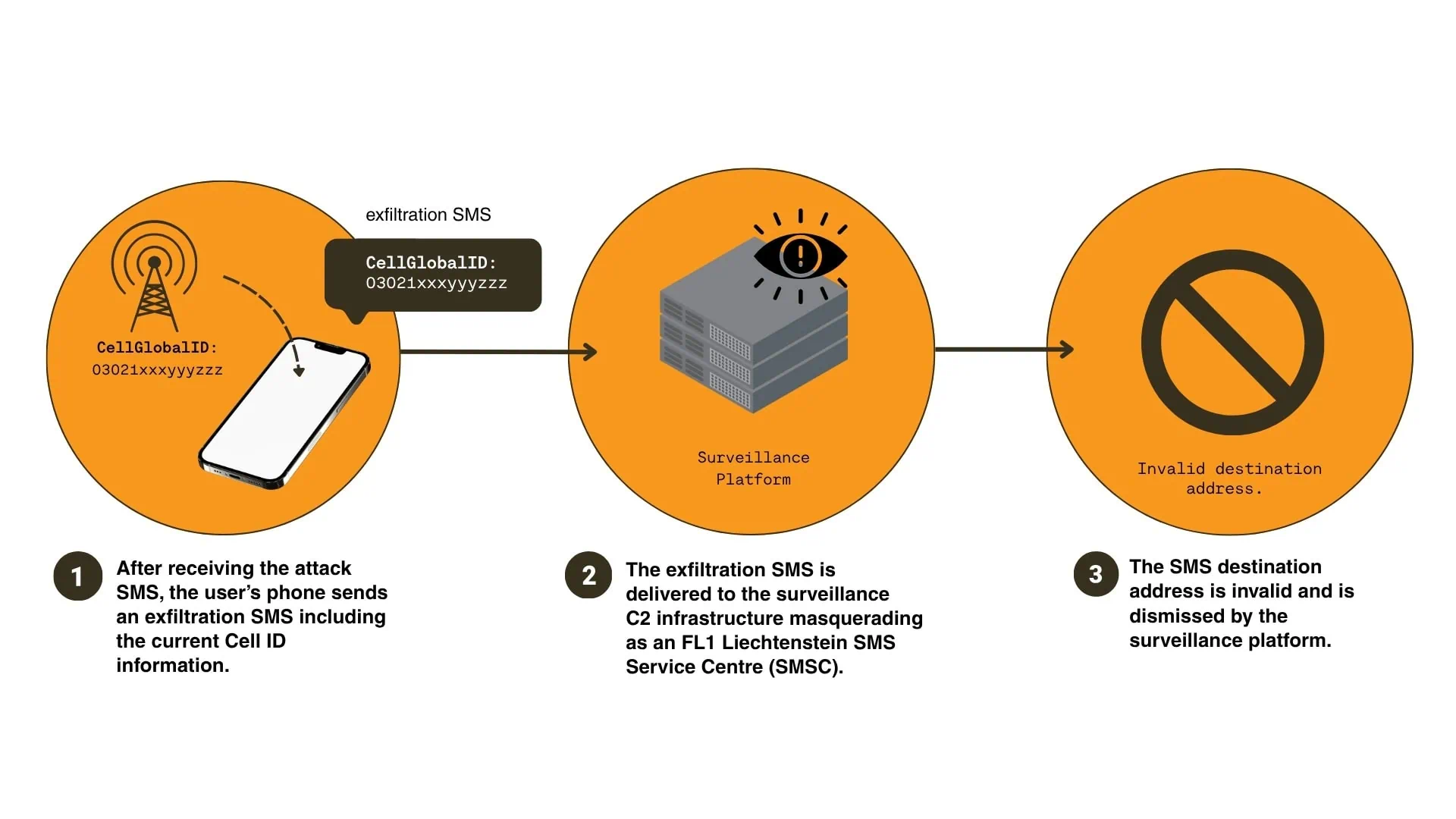
3. The Exfiltrated Data
The location data transmitted in the SMS is retrieved via the Provide Local Information command and stored in variable 0x17. The Concatenate Values command appends a distinct Length Byte with the value 0x0a (step 5 in Figure 10), indicating that the final three bytes of the SMS were likely used as Artificial Padding to fill empty space.
Through the Initialize Variable and Concatenate Values commands, attackers construct an exfiltration SMS containing location information and a destination address that is likely used as an Identifier for the target rather than a genuine delivery endpoint.
Comparison with SIMjacker
The attack SMS sent by STA2 aligns with the typical configuration of a SIMjacker SMS (as described in a 2019 report by ENEA). A comparison of the commands used reveals subtle differences. Nevertheless, ENEA notes that real-world SIMjacker SMS messages also exhibit Variations and modifications. The attack SMS observed in this investigation could be a newer Variant of SIMjacker, adapted to SIM card or operator configurations to improve its Efficacy. These differences are listed in Table 10.
| Feature | Observed Attack SMS (STA2) | Typical SIMjacker SMS | Additional Details |
|---|---|---|---|
| Variable Reset | The Card element is not configured to Reset all variables in the S@T browser. | Resetting variables is performed. | Resetting all variables was observed in over 44% of SIMjacker SMS messages analyzed by ENEA. |
| Command Sequence | First obtains location information, then constructs the SMS-SUBMIT header. | First creates the SMS-SUBMIT header, then retrieves location information and phone IMEI. | – |
| Data Extraction | Collects phone location, but does not collect IMEI. | In 93% of tracked SIMjacker SMS messages, both location and IMEI of the target device are collected. | – |
| Variable with Filler Bytes | Does not include a dedicated variable with Filler bytes; rather, uses Single bytes added during the Concatenation phase. | Often includes a variable with filler bytes placed in various locations within the data extraction SMS. | This (in common versions) is likely done to Obfuscate the message. |
Comparison of the observed attack SMS with common SIMjacker messages.
Use of a Swedish Operator Identifier as an Entry Point
The first two messages sent by STA2 used the identical operator GT numbered 467647531812; confirming the use of this identifier as the address of a Command and Control (C2) endpoint.
Using a public numbering plan search tool provided by PTS (the Swedish Post and Telecom Authority) (referencing Figure 12), researchers confirmed that this number falls within the range assigned to Telenabler AB.
Telenabler is a network provider offering services to Mobile Virtual Network Operators (MVNOs). Describing its activities, Telenabler’s website states: “We are experts in dealing with different country-specific telecom regulations and partner with some of the strongest telecom partners in the world.”
Citizen Lab previously reported on Telenabler’s Global Title (GT) leasing business model in its 2023 “Finding You” report. In that report, this exact GT was identified as an originating address repeatedly discovered in location tracking operations.
Since the publication of that report, activities associated with the address 467647531812 have not ceased; furthermore, between October 2023 and April 2025, the research team identified over 1,700 additional SS7 attacks originating from this address, with more than 92% of its traffic directly linked to location tracking. The primary types of SS7 queries observed included provideSubscriberInfo (1,011 instances) followed by provideSubscriberLocation (386 instances).
The repeated and exceptionally high-volume use of this GT alongside various types of location queries clearly indicates that this identifier is specifically allocated and used for Surveillance Purposes.
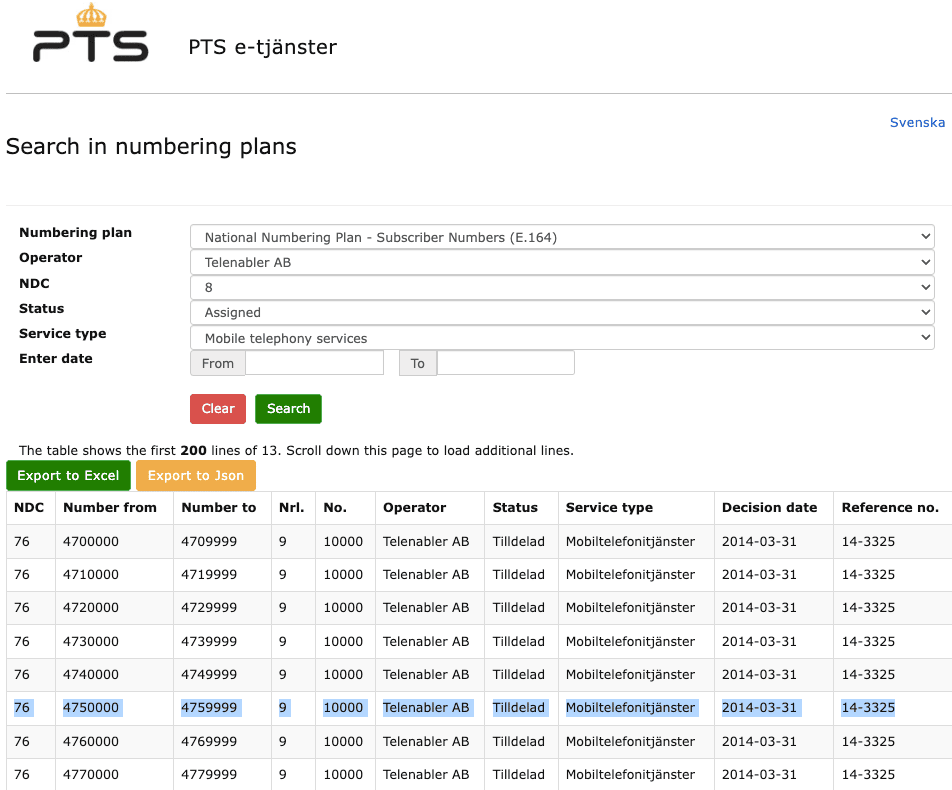
SIMjacker Payload Exposes a Coordinated Attack Cluster
The signaling identifiers used in the SIMjacker exploit constituted the Endpoints for Command and Control (C2) communication. This attack utilized three numbers belonging to different operators, each playing a unique role in the attack, revealing tradecraft that demonstrates STA2’s precise and deep knowledge of the operator routing and interconnect ecosystem.
-
GT Address for Payload Delivery:
467647531812– Assigned to Telenabler Sweden -
SMSC GT Address Used for Location Data Exfiltration:
423790105651– Assigned to FL1 Liechtenstein -
Spoofed Sender SMS Address:
250730091970– Assigned to Airtel Rwanda
Mobile operators allocate GT address ranges to specific core network functions (such as SMSC, HLR, MSC, etc.) and publish these allocations in IR.21 documents to ensure service accessibility and proper signaling traffic routing. Because GTs are Routable signaling identifiers, they play a central role in roaming and establishing trust between operators. Many operators rely on published IR.21 address allocations to enforce their security policies, Rejecting signaling messages whose origins do not match network allocations or service functions.
The GT address used in this attack (423790105651) falls within a range of addresses allocated to SMSCs by the FL1 operator (as shown in their IR.21 document in Figure 13). However, the configured address used in the attack contains an Extra Digit beyond the documented range; indicating the attacker’s precise knowledge and awareness of FL1’s IR.21 allocations.
Appending this extra digit ensures that the Exfiltration SMS is correctly routed toward the actor’s surveillance C2 infrastructure. Simultaneously, this extra digit serves as an internal identifier for the surveillance application, tagging the message as a SIMjacker operation to process the target device’s location information within it.
![]()
Use of Spoofed Address for SMS Sender (Airtel Rwanda) The address 250730091970, used as the SMS sender in the SIMjacker attack, Maps to a range of GTs belonging to Airtel Rwanda, but does not appear to be assigned to any specific network function. However, the attack history associated with this GT shows that since 2022, it has been used in over 600 events exclusively for location tracking operations.
Attribution Assessment
The STA2 campaign represents a unique approach in telecom surveillance, combining SS7 signaling, SIM-based exploits, and Diameter-based location tracking techniques. While this report does not directly attribute these activities to a specific organization, their operational model has been matched based on historical attack data as well as technical and behavioral indicators.
A Long History of Network Surveillance
To assess the scale of STA2’s activities, researchers analyzed historical SS7 and Diameter firewall telemetry associated with the Cluster of operator identifiers used in this campaign. This review revealed a highly Prolific Operation with over 15,700 location tracking attempts dating back to October 2022.
A sample of early activities is shown in the screenshot in Figure 14 of the report. This image depicts a captured sequence of tracking messages on October 19, 2022, utilizing identities from multiple operators. All of these instances used the identical Origin-Host format (displayed in the “Source Node” column) and the Route-Record corresponding to Jersey-Airtel. (Note: The target user’s IMSI and portions of the IPX provider Hostnames have been partially redacted and obscured for privacy reasons.)
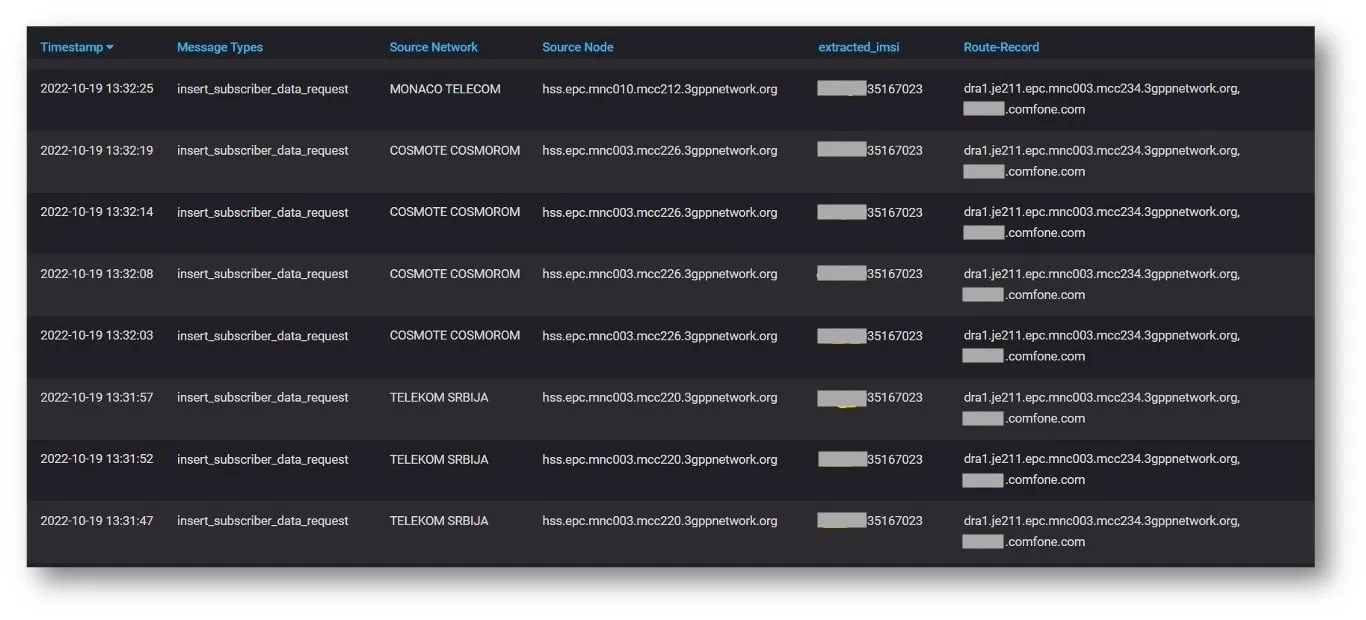
Table 11 summarizes the volume and evolutionary trajectory of STA2’s surveillance activities over time.
| Protocol | October 2022 | 2023 | 2024 | 2025 |
|---|---|---|---|---|
| Diameter | 10 | 96 | 973 | 2622 |
| SS7 | 10 | 399 | 392 | 1891 |
Evolutionary trajectory of multi-year surveillance activities attributed to STA2.
Amidst this attack history, researchers searched for indicators that might point to a known surveillance actor. The attack history associated with the GTs revealed connections to Fink Telecom Services (FTS); a Switzerland-based telecom provider that had been exposed as a commercial vendor of telecom surveillance systems in joint investigative reports by Lighthouse Reports and Bloomberg. Those reports found clusters of attacks using the exact same Signatures as the STA2 group.
FTS Signaling Overlap
STA2’s surveillance activities exhibit significant alignment with identifiers and patterns associated with FTS; including simultaneous (same-day) location tracking attacks and matching Diameter Hostname formats. Researchers analyzed a history of attacks beginning in November 2022 that linked both FTS and STA2.
Prior to media reports connecting FTS to SS7-based surveillance, the research team had identified multiple STA2 surveillance operations indirectly linked to FTS; many of these occurred on the exact same day targeting the same subjects. A sample of these attacks is listed in Table 12.
| Date | Source Node | Network | Country | Threat Type | Signaling Operation |
|---|---|---|---|---|---|
| 4-Dec-22 | hss.epc.mnc001.mcc260... |
POLKOMTEL | Poland | Location Discovery | Insert-Subscriber-Data-Request |
| 4-Dec-22 | 46727507103 | FINK TELECOM SERVICES | Sweden | Location Discovery | provideSubscriberInfo |
| 15-Dec-22 | 250730091970 | AIRTEL RWANDA | Rwanda | Location Discovery | provideSubscriberInfo |
| 15-Dec-22 | 25671000034 | UGANDA TELECOM | Uganda | Location Discovery | provideSubscriberInfo |
| 15-Dec-22 | 26482000011 | DEMSHI TELECOM | Namibia | Location Discovery | provideSubscriberInfo |
| 18-Dec-22 | 250730091970 | AIRTEL RWANDA | Rwanda | Location Discovery | provideSubscriberLocation |
| 18-Dec-22 | 25671000034 | UGANDA TELECOM | Uganda | Location Discovery | provideSubscriberLocation |
| 19-Dec-22 | 79588879810 | LETAI | Russia | Location Discovery | anyTimeInterrogation |
| 19-Dec-22 | 26482000011 | DEMSHI TELECOM | Namibia | Location Discovery | anyTimeInterrogation |
| 19-Dec-22 | 250730091970 | AIRTEL RWANDA | Rwanda | Location Discovery | anyTimeInterrogation |
| 14-Feb-23 | 26482000011 | DEMSHI TELECOM | Namibia | Location Discovery | provideSubscriberInfo |
| 14-Feb-23 | hss.epc.mnc001.mcc260... |
POLKOMTEL | Poland | Location Discovery | Insert-Subscriber-Data-Request |
| 14-Feb-23 | 250730091970 | AIRTEL RWANDA | Rwanda | Location Discovery | provideSubscriberInfo |
| 11-Mar-23 | hss.epc.mnc063.mcc240... |
FINK TELECOM SERVICES | Switzerland | Location Discovery | Insert-Subscriber-Data-Request |
| 11-Mar-23 | hss.epc.mnc001.mcc649... |
MTS | Namibia | Location Discovery | Insert-Subscriber-Data-Request |
| 5-Apr-23 | 4672750710 | FINK TELECOM SERVICES | Sweden | Location Discovery | provideSubscriberInfo |
| 5-Apr-23 | 25671000034 | UGANDA TELECOM | Uganda | Location Discovery | provideSubscriberInfo |
| 5-Apr-23 | hss.epc.mnc001.mcc260... |
POLKOMTEL | Poland | Location Discovery | Insert-Subscriber-Data-Request |
| 16-Aug-23 | hss.epc.mnc001.mcc260... |
POLKOMTEL | Poland | Location Discovery | Insert-Subscriber-Data-Request |
| 16-Aug-23 | hss.epc.mnc063.mcc240... |
FINK TELECOM SERVICES | Switzerland | Location Discovery | Insert-Subscriber-Data-Request |
| 23-Feb-24 | 467647531812 | TELENABLER AB | Sweden | Location Discovery | provideSubscriberInfo |
| 23-Feb-24 | 250730091970 | AIRTEL RWANDA | Rwanda | Location Discovery | provideSubscriberInfo |
| 23-Feb-24 | 264820000458 | DEMSHI TELECOM | Namibia | Location Discovery | provideSubscriberInfo |
Firewall telemetry showing addresses associated with Fink Telecom Services and STA2.
The attacks summarized in Table 12 include identifiers observed in the STA2 campaign positioned alongside GT and Diameter identifiers attributed to FTS.
Notably, the Diameter Hostname formats used in STA2 attacks also utilize the MCC/MNC values associated with FTS. These registered values published in IR.21 documents are shown in Figure 15 of the report.
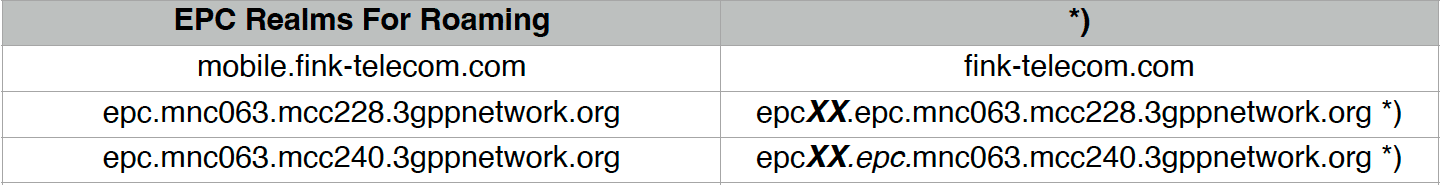
While identity Spoofing cannot be entirely ruled out, the alignment of historical location tracking attacks on the exact same day, the Diameter Hostname formats used in the STA2 campaign, the GT ranges published in FTS’s IR.21 documents, as well as reports published by journalists exposing SS7 attacks attributed to FTS, all point to clear and apparent links between STA2 and FTS.
Conclusion
This report is the first investigation to Map live telemetry of SS7 and Diameter attacks to the operator identifiers and interconnect paths used in Cross-protocol mobile surveillance operations.
Rather than implanting Spyware on devices or hacking enterprise networks to conduct mobile espionage, these two threat actors exploited legitimate operator signaling identities and trusted interconnections to conduct targeted surveillance across national borders. By blending and concealing their location queries within normal roaming traffic, and manipulating protocols and network identifiers, they effectively operated as “Ghost Operators” within the global telecom ecosystem.
The findings of this report demonstrate how advanced actors Operationalize telecom infrastructure to execute campaigns that persist for years without detection. Telecommunications networks form the Backbone of global civil society; when the principle of “trust” is abused for surveillance purposes, the consequences extend beyond targeted victims to encompass mobile users worldwide.
This investigation exposes more than just protocol vulnerability issues in telecommunications; it highlights Governance Failures across the interconnect ecosystem used for critical mobile communications. This report also shows how these weaknesses have enabled the use of telecom infrastructure as a Covert Surveillance Platform.
The global telecommunications ecosystem can no longer rely on Legacy Trust Models. Without mandatory Authentication, enforceable interconnect controls, transparency in commercial network access, and Regulatory Accountability, mobile networks will continue to be abused as a global platform for covert espionage.

